In immediately’s computing atmosphere, firmware can imply a number of issues, starting from a whole working system in embedded gadgets to a small flash program in a {hardware} part that tells your working system (OS) about that {hardware}’s capabilities. On this weblog submit, we’ll give attention to the vulnerabilities within the latter sort of firmware popularized by the Uniform Extensible Firmware Interface (UEFI). I’ll discover how these vulnerabilities are a profitable goal for high-profile attackers, similar to nation-states which are in search of vulnerabilities within the less-visible parts of immediately’s computing atmosphere.
First, to get our footing, you will need to perceive what UEFI actually is. UEFI replaces the legacy Primary Enter/Output System (BIOS), interfacing {hardware} to the OS and offers an extensible intersection between {hardware} and the OS itself. The UEFI customary additionally identifies dependable methods to replace this firmware from the OS. In essence, in immediately’s computer systems, there’s one other layer of software program that may assist the OS perceive and use out there {hardware}. In fact, this important layer of software program faces all of the challenges of immediately’s software program: bugs, safety points, patching, and upkeep. It additionally lacks visibility, making it exhausting for defenders to guard this a part of their computing environments from ever-increasing threats.
Moods of your CPU: Actual, Protected, and System Administration
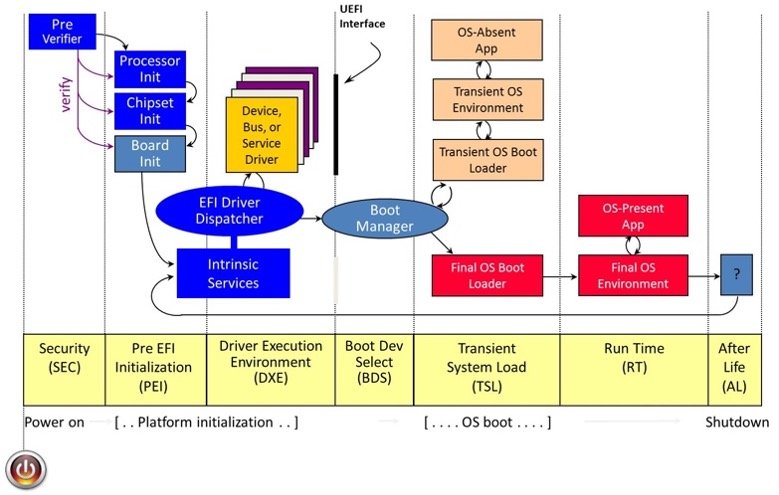
The Intel CPU structure defines a number of modes through which the CPU operates to interpret, execute, and fulfill the duties requested by the OS. In most fashionable working programs, protected mode offers for safe operations of duties with capabilities, similar to reminiscence isolation between processes. Intel additionally offers a system administration mode (SMM), which is a extremely privileged mode of operation accessible to the OS through the particular System Administration Interrupt (SMI) handler. SMM is the first mode through which UEFI operates to interface straight with the {hardware}. Sometimes, a single grasp SMI handler will permit for registration and administration of different SMI handlers, that are all recognized by their globally distinctive identifiers (GUIDs).
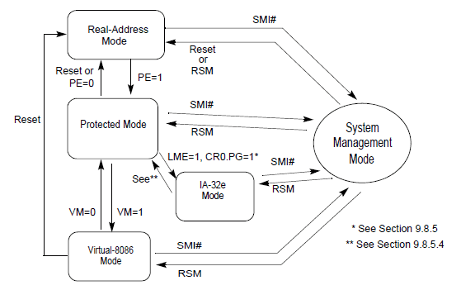
Determine 1: Picture from Intel’s CPU handbook
What Can Be Smaller than 0? Properly –2 Perhaps?
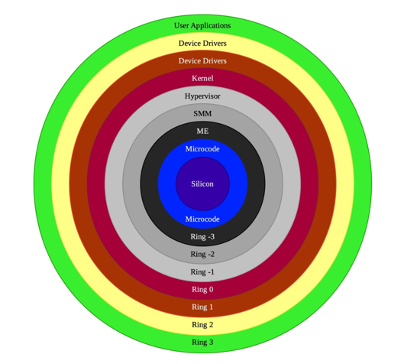
In pc science, safety rings are used to determine numerous ranges of privileged entry to assets in your pc. Ring 0 is usually thought of to be the best degree of entry out there to a system-level consumer of an OS. Nonetheless, hidden rings (Ring –1 for hypervisor and Ring –2 for SMM) are primarily required to carry out duties with privileges larger than the OS itself. These embrace duties similar to configuring or modifying the configuration of the {hardware} or including new software-based capabilities to an already current {hardware} gadget.
In sure circumstances, there are additionally issues, similar to UEFI variables, that present vital knowledge used all through the OS boot course of. The UEFI customary spells out specs for SMI handlers, that are mainly software program written to realize system calls to request the CPU to carry out duties within the excessive privilege mode referred to as SMM. Vulnerabilities exist each within the programming of the SMI handler and in correctly defining (and defending) UEFI variables. These actors who can exploit these vulnerabilities are supplied with a excessive privilege mode to execute their code on a focused pc.
Software program Means Vulnerabilities
As UEFI capabilities are developed, increasingly more functionality is delegated to the UEFI software program to permit it to change, customise, and in some circumstances, improve at the moment out there {hardware} capabilities of a pc. Most of this software program is written in lower-level languages (largely C) that require cautious use of assets, similar to reminiscence. All of the operations in SMM are saved in a protected space of reminiscence referred to as SMRAM, which is remoted from the working system. The communications initiated by the SMI handlers are abstracted utilizing a communications buffer dubbed CommBuffer. SMRAM additionally has particular code segments (non-writeable) and knowledge segments (non-executable), that are all invoked from the OS utilizing a CommBuffer.
At present, software program anticipated to run with SMM’s privileged mode is offered by a number of distributors and finally ends up being assembled by an OEM PC vendor earlier than a pc is offered out there. Nearly all of this software program is derived from the instance community-developed mission referred to as Tianocore that gives software program growth kits (SDK) referred to as EDKII for constructing these UEFI modules. EDKII is instance code that requires cautious safety evaluation, particularly of reminiscence administration, earlier than being carried out for particular use circumstances. Many well-known C coding errors (e.g., unsafe pointers, correct pointer validation, sort confusion, and improper locking) will be simply launched whereas growing UEFI software program. These defects lead the software program to reveal SMRAM contents, corrupt the SMRAM payload, hijack the SMM code circulate, and at last, allow the writing arbitrary code/content material to the Serial Peripheral Interface (SPI) Flash. As a mixed impact, these errors give the attacker a strong approach to write everlasting code on the gadget in a most obscure location.
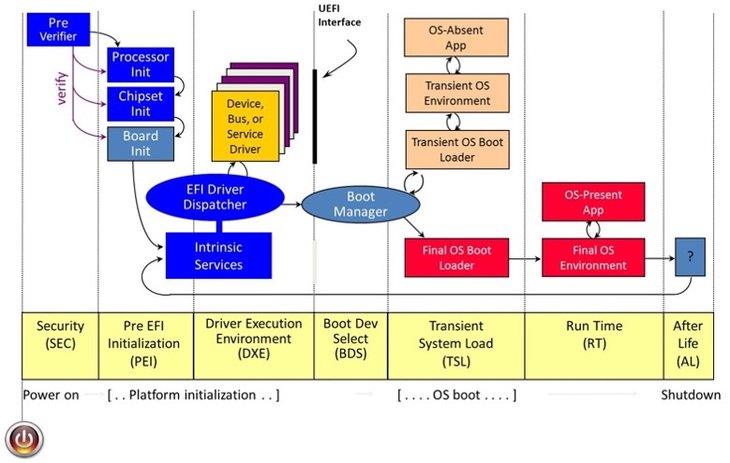
The platform-initialization part diagram from the EDKII Construct Specification repository offers some detailed info on how a contemporary pc goes by means of its boot course of. UEFI offers immense capabilities to provoke, configure, and customise the way in which through which {hardware} might be used when the pc is working in regular circumstances. This highly effective functionality is now being explored by each safety researchers and attackers.
For instance, researchers Assaf Carlsbad and Ittai Liba from Sentinnel One disclosed the power to interrupt safe boot to compromise one of many earliest phases of platform initialization. The researchers demonstrated the exploitation of a number of weaknesses ranging from a scarcity of validation of SMRAM contents on account of nested tips to overwrite the secure-boot configuration. In one other current disclosure, researcher Alex Matrsov from Binarly disclosed a lot of SMI handlers that primarily permit privilege escalation within the Drive eXecution Surroundings (DXE) part that may result in arbitrary code execution in excessive SMM privilege mode of the CPU. These assaults may also be initiated as your pc is reawakened from sleep mode. The systemic errors mentioned above make every part within the boot course of weak to assault.
Why Assault the SMM?
Ought to we be involved about these vulnerabilities? Do attackers actually need to undergo 1000’s of UEFI implementations to search out vulnerabilities? SPI Flash communications may be very gradual in comparison with immediately’s widespread assaults, which goal reminiscence and disk as places for permanence or persistence. Will attackers goal such a gradual SPI interface for assaults? Beneath are simply a number of the explanation why attackers discover UEFI implementations to be a gorgeous goal for assaults:
- SMM because the excessive floor—SMM provides the attacker highest privilege mode of a CPU, nearly unguarded even by the working programs (Ring 0), hypervisor (Ring –1), and any safety software program together with endpoint detection and response (EDR) in immediately’s computing environments.
- P is for persistence in APT—The attacker immediately is in search of persistence that may survive rebuilding of the working system. What higher place is accessible than the SPI flash? Mainly the BIOS location. Lojax and Sednit, for instance, goal SPI flash for persistence.
- Invisibility—As proven by MoonBounce, an implant written as a UEFI firmware module can work in stealth leaving no hint for the OS or generally even the community.
- A damaged vulnerability lifecycle—Many firmware vulnerabilities both aren’t addressed, or they reappear a number of years after discovery. Advanced provide chain and poor firmware replace cycles make UEFI firmware a really perfect goal for attackers to contemplate when growing implants.
What Ought to We Do?
A number of efforts are already underway in analysis and business to enhance UEFI safety. Listed here are just a few efforts that we wish to turn out to be concerned in.
- Finest practices and higher instruments for UEFI growth—The EDKII specification and a pattern implementation have been very highly effective in onboarding a lot of small corporations for UEFI growth. Nonetheless, a lot of safe coding practices and audits are wanted to make sure that code is protected towards typical abuse of reminiscence primitives in these low-level applications. Analysis and energy are wanted to safe the code by default limiting SMRAM abuse. There’s additionally a necessity for DevSecOps-like efforts to make sure that the firmware growth lifecycle is secured at its very starting.
- SBOM and transparency–—A lot of the UEFI growth and manufacturing of UEFI modules and firmware have been carried out privately by a number of distributors of the provision chain referred to as impartial BIOS distributors (IBV), impartial {hardware} distributors (IHVs), and unique gadget producers (ODMs). Nearly all of these software program modules are protected by proprietary storage and compression methods, which offer very low visibility to prospects and generally even to the OEMs that bundle and resell the software program. The UEFI firmware area wants a clear and accountable software program invoice of supplies (SBOM) with ample element to assist accountable disclosure of parts and vulnerability administration of those parts.
- Instruments to investigate UEFI photos, modules, and capsules—Considerably associated to the sooner concern of transparency, a lot of the UEFI code is opaque and generally even obfuscated by their distributors. We due to this fact want extra clear instruments to investigate and audit UEFI firmware developed both as a supply code or as binary static code analyzers to determine code circulate and potential abuse of supposed UEFI standards-based communications and executions. At present just a few software program instruments, similar to Chipsec, permit the dumping of ROM EFI photos. Some reverse-engineering instruments, similar to Sentinel’s Brick and Binarly’s efiXplorer, exist to investigate UEFI software program modules. The shortage of such instruments limits the quantity of neighborhood evaluation and perception wanted to find and deal with safety issues in UEFI software program.
- Well timed vulnerability lifecycle administration—UEFI firmware vulnerabilities discovery, accountable disclosure of those vulnerabilities, and well timed software program updates to handle these vulnerabilities will all should be improved. Capabilities, similar to automated updates and capsule-based updates, needs to be commonplace to make sure that UEFI updates aren’t cumbersome or complicated for the customers and customers of computing environments. Efforts, similar to Microsoft’s Firmware Replace Platform and Linux Vendor Firmware Service (LVFS) initiatives, try to resolve this by offering a safe approach to replace firmware capsules utilizing a standards-based strategy. LVFS specifically offers an open-source, clear approach to deal with this difficulty by lowering the burden of delivering the firmware updates on distributors. OEM distributors are urged to actively take part in such efforts to make sure well timed replace of vendor firmware modules.
Addressing Systemic Courses of Vulnerabilities
On the SEI’s CERT Division, we see UEFI safety as intently associated to our analysis in addressing systemic courses of vulnerabilities. We wish to accomplice and assist your efforts by offering assist for well timed disclosure, higher evaluation, and a swift response to vulnerabilities within the UEFI software program ecosystems. In case you are excited by working with us, please e mail data@sei.cmu.edu.