Tales from the SOC is a weblog collection that describes latest real-world safety incident investigations carried out and reported by the AT&T SOC analyst group for AT&T Managed Prolonged Detection and Response clients.
Govt abstract
Since mid-June 2022, AT&T Managed Prolonged Detection and Response (MXDR) Safety Operations Heart (SOC) noticed an infinite variety of assaults from Mirai botnet-C2 trying to realize entry to SSH servers as an alternative of Telnet.
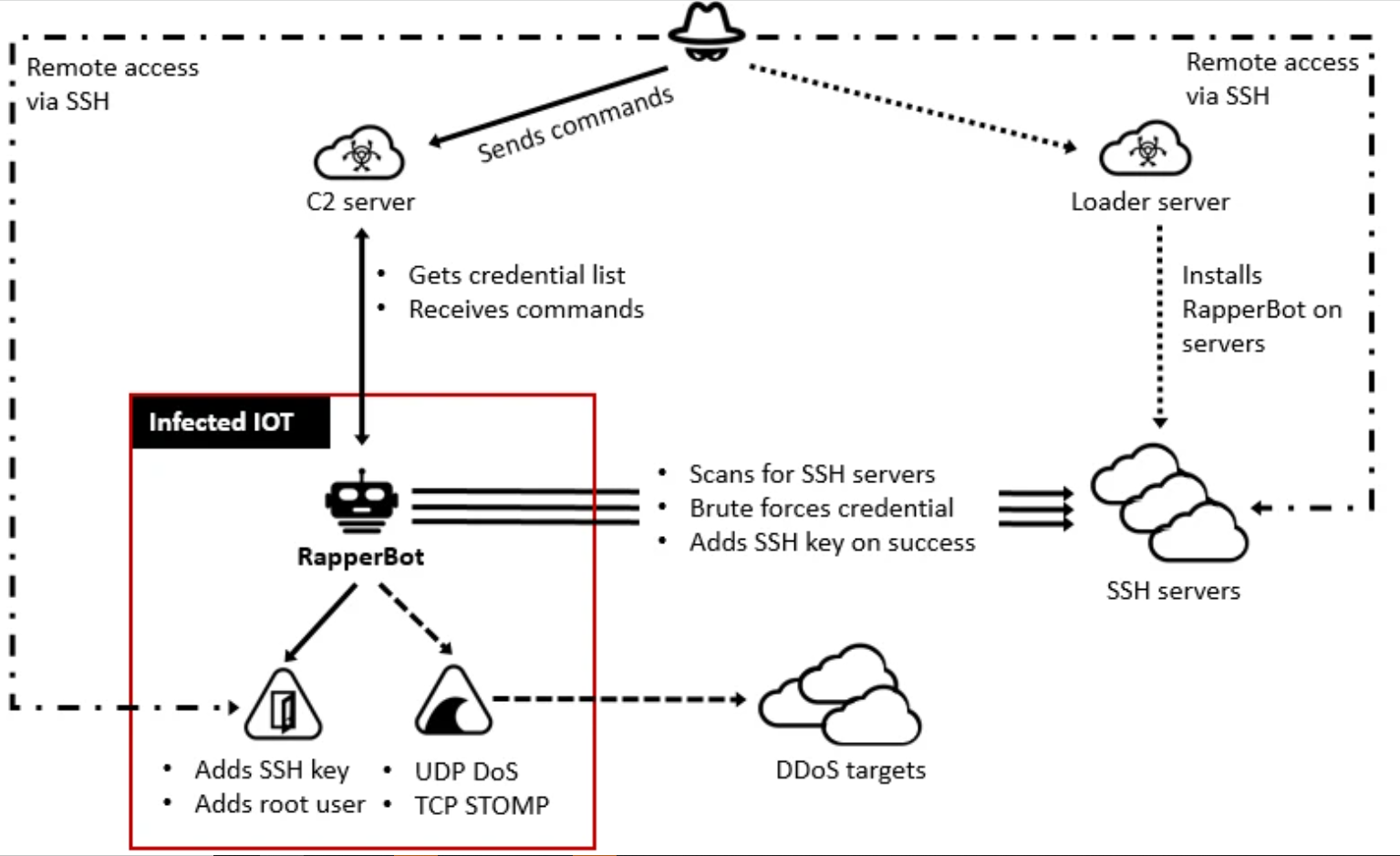
Because of the varied techniques, methods, and procedures (TTP) noticed, this assault has been related to RapperBot botnet (Mirai variants.) RapperBot’s aim remains to be undefined.
In accordance with the evaluation that was revealed by FortiGuard Labs, whereas the vast majority of Mirai variants can naturally brute power Telnet servers that use default or weak passwords, RapperBot specifically scans and makes an attempt to brute power SSH servers which are designed to require password authentication.
A big a part of the malware is executing an SSH 2.0 shopper which is ready to join and brute power any SSH server utilizing Diffie-Hellman key alternate with 768-bit or 2048-bit keys and information encryption utilizing AES128-CTR. A singular attribute of brute forcing in RapperBot is the usage of SSH-2.0-HELLOWORLD with the intention to determine itself to the focused SSH server throughout the SSH Protocol Trade part.
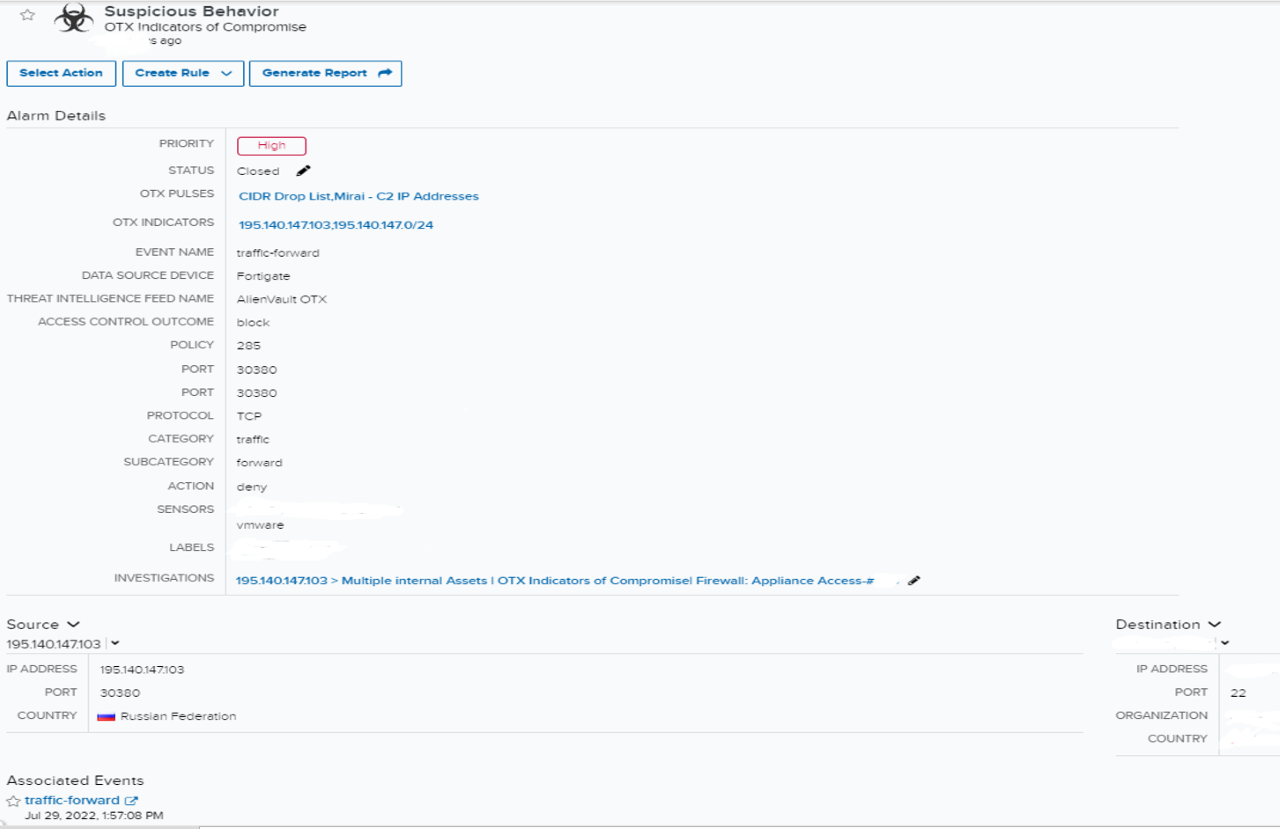
One of many malicious Mirai botnet IP addresses had allowed community site visitors with an asset in a corporation over SSH port 22. After some information transferring, the session closed with the client-reset motion. The MXDR SOC group rapidly recognized and advisable mitigation steps to stop lateral motion and the attacker going additional.
Investigation
Preliminary alarm evaluate
Indicators of Compromise (IOC)
The alarm initiated with the a number of Open Risk Trade (OTX) pulses (Miraibotnet-C2- CDIR Drop Record) and an OTX indicator of a recognized malicious IP. There was community site visitors between the recognized malicious IP and a public IP of an inside asset in a corporation. The community site visitors was over SSH port 22, and the safety system (firewall) motion was a deny. The safety system (firewall) deny motion was proof of the auto-mitigation. On this case, auto-mitigation means the assault is prevented by firewall guidelines and menace intelligence by denying the connection from malicious IP.
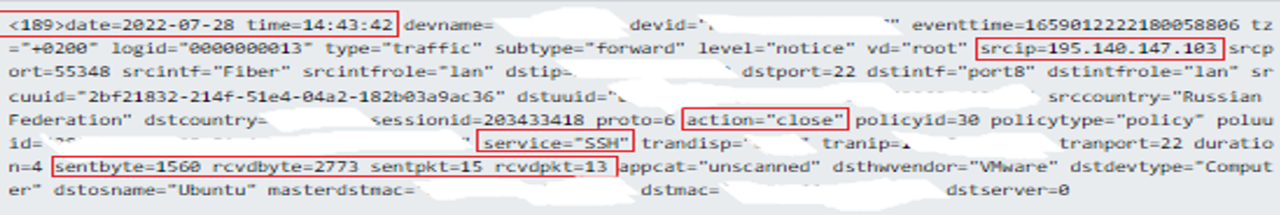
Nevertheless, additional evaluation of the occasions confirmed that the site visitors was allowed from the malicious IP to a different inside asset. Along with this, there have been indicators of knowledge switch from supply IP with “sentbyte=1560, rcvdbyte=2773, sentpkt=15, rcvdpkt=13”
** Threat mitigation in Cybersecurity is the discount of the general danger/influence of cyber-attacks. Detection, prevention, and remediation are three parts of danger mitigation in cybersecurity.
Expanded investigation
Occasions search
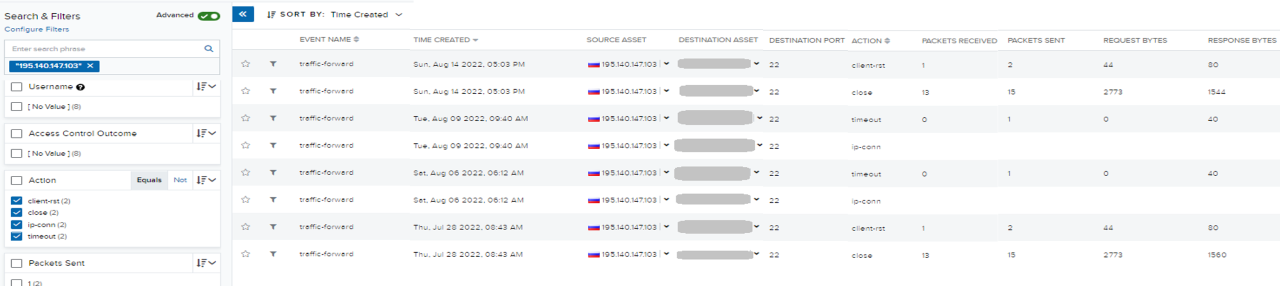
After checking occasions related to the alarm, the group at all times checks the environmental safety to see if the malware had additional penetrated the setting or tried any lateral motion.
The group searched occasions by pivoting on the indicator IP, filtering the previous 90 days of occasions, and the safety system (firewall) allowed motion sorts. It was decided that there have been just a few connections from malicious IP to completely different inside property with the client-rst, server-rst, timeout, and closed occasions.
Client-rst – Session reset by shopper, Server-rst – Session reset by server
These are often session finish causes that present who’s sending TCP (Transmission Management Protocol) reset and the session terminates – so this doesn’t imply {that a} safety system (firewall) is obstructing the site visitors. It means after a session is began between client-to-server, it’s terminated by (shopper or server), relying on who despatched the TCP reset. Session-end outcomes might be present in site visitors logs.
The group suspected that the system may be compromised as a result of the session was reset from the shopper facet (which is the adversary facet.) It was then noticed that the session was closed (terminated) with a considerable amount of packet transmissions.
Occasion deep dive
After additional examination of the allowed connections, the malicious IP confirmed site visitors with the client safety system (firewall) over SSH port 22. SSH port 22 makes use of a TCP connection. Subsequently, earlier than transferring information it wants to determine a dependable reference to the 3-way handshakes.
With a view to handshake the header (first two packets), TCP makes use of roughly 24 bytes and for regular transmission of packet about 20 bytes. Establishing a dependable reference to 3-way handshake wants simply three packets to be transmitted. Establishing a connection: ~ 128-136 bytes.
One other statement is that the despatched and obtained bytes with the packet measurement are indicators of knowledge transferring because of the packets and bytes being greater than regular packets and bytes of TCP 3-way handshake. That is believed to be a sign of a payload or compromised credentials.
Rapperbots work like an SSH brute-forcing marketing campaign. After it has gained entry on a tool, it sends its structure to the C2 server – the gadget’s IP, and the credentials used. Then the adversary tries to load the primary payload binary on the compromised gadget through binary downloader or software program like ftpget, wget, curl, or tftp, that’s put in on the gadget.
Reviewing for added indicators
At this level, the attacker tried to get “Preliminary Entry (tactic)” into the community through the use of “Exploit Public Dealing with Software” approach based mostly on the Mitre Att&ck Framework.
Exploit Public Dealing with Software is a method which is utilized by adversaries to benefit from vulnerabilities/weaknesses in a program or web going through pc to realize Preliminary entry to a community. On this case, despite the fact that there was proof of knowledge switch, proof of payload or lateral motion exercise weren’t seen.
Response
Constructing the investigation
An investigation was created by following the incident response course of. The investigation included figuring out the incident, discovering the basis reason behind the incident and Indicators of compromise. Then we made suggestions to the client on mitigation/remediation steps. We communicated with the client to make sure crucial actions are executed. Really helpful mitigation steps had been:
- Blocking the malicious IP
- Disabling SSH password authentication (if attainable)
- Altering passwords to stronger passwords for the gadget.
Incident response is an organizationed method and course of to handle cybersecurity breaches/incidents or cyberattacks. It contains a number of steps:
- Figuring out an incident/assault
- Minimizing injury
- Eradicating the basis trigger
- Minimizing restoration value and time
- Studying classes from the incident
- Taking preventative motion
In accordance with the evaluation that was revealed by FortiGuard Labs, Rapperbot builders improved their code to take care of persistence, which differentiates it from different Mirai variants. Even after rebooting contaminated property or eradicating malware, intruders can constantly entry contaminated property through SSH. Subsequently, rebooting the gadget or eradicating malware Just isn’t a everlasting mitigation possibility.
The Rapperbot’s main menace is brute forcing the credentials of SSH. By disabling SSH password authentication (if attainable), or altering passwords to stronger passwords for the gadget, the Rapperbot mitigation can simply be carried out.
Buyer interplay
The client needed to be stored within the loop and knowledgeable if the assault continues.
Limitations and alternatives
Limitations
On this investigation, MXDR was unable in a position to see contained in the transmitted packets. Because of the dearth of visibility into the community flows within the setting, MXDR has restricted entry to the client setting. Nevertheless, MXDR suspected the information switch might embody the primary payload binary on the compromised gadget.