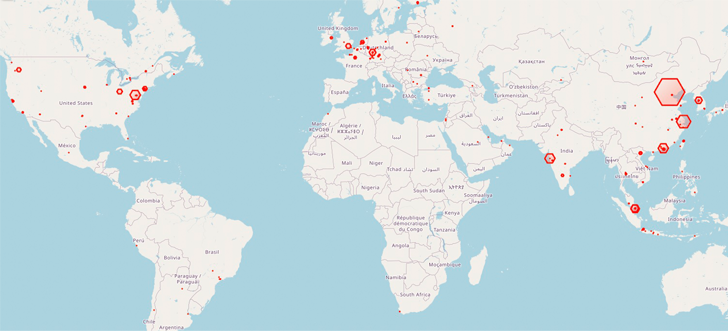
At the very least 1,200 Redis database servers worldwide have been corralled right into a botnet utilizing an “elusive and extreme menace” dubbed HeadCrab since early September 2021.
“This superior menace actor makes use of a state-of-the-art, custom-made malware that’s undetectable by agentless and conventional anti-virus options to compromise numerous Redis servers,” Aqua safety researcher Asaf Eitani stated in a Wednesday report.
A big focus of infections has been recorded in China, Malaysia, India, Germany, the U.Ok., and the U.S. thus far. The origins of the menace actor are presently unknown.
The findings come two months after the cloud safety agency make clear a Go-based malware codenamed Redigo that has been discovered compromising Redis servers.
The assault is designed to focus on Redis servers which might be uncovered to the web, adopted by issuing a SLAVEOF command from one other Redis server that is already underneath the adversary’s management.
In doing so, the rogue “grasp” server initiates a synchronization of the newly hacked server to obtain the malicious payload, which incorporates the subtle HeadCrab malware onto the latter.
“The attacker appears to primarily goal Redis servers and has a deep understanding and experience in Redis modules and APIs as demonstrated by the malware,” Eitani famous.
Whereas the final word finish purpose of utilizing the memory-resident malware is to hijack the system assets for cryptocurrency mining, it additionally boasts of quite a few different choices that enables the menace actor to execute shell instructions, load fileless kernel modules, and exfiltrate information to a distant server.
What’s extra, a follow-on evaluation of the Redigo malware has revealed it to be weaponizing the identical master-slave method for proliferation, and never the Lua sandbox escape flaw (CVE-2022-0543) as beforehand disclosed.
Customers are really useful to chorus from exposing Redis servers on to the web, disable the “SLAVEOF” characteristic of their environments if not in use, and configure the servers to solely settle for connections from trusted hosts.
Eitani stated “HeadCrab will persist in utilizing cutting-edge strategies to penetrate servers, both by exploiting misconfigurations or vulnerabilities.”