To place community operations in context, analysts want to trace the software program working on the group’s community. This monitoring includes not solely protecting tabs on which purposes are working, however whether or not these purposes are being frequently up to date in variations and patches. Many safety checklists advocate protecting software program present on relevant latest variations and patches. Such suggestions, together with RFC 2196, below “ongoing actions,” have been in place for many years. DHS/CISA suggestions on defending towards present ransomware threats emphasize protecting your laptop patches updated. Some organizations push updates onto inner purchasers and servers, however others use vendor-supported replace companies. This weblog submit presents an analytic for monitoring software program updates from official vendor places.
There are a selection of ways in which monitoring updates helps to tell community safety efforts. Utilizing vendor-supported replace companies could require purchasers and servers to ballot designated obtain websites for probably the most present updates. By understanding which hosts are receiving updates, analysts can observe compliance with the group’s replace insurance policies. Monitoring which updates the purchasers and servers are receiving additionally helps affirm the software program configuration on these gadgets, which in flip could feed into the community vulnerability administration course of. Lastly, monitoring the dates at which updates happen helps to determine how present the configured software program is on the group’s purchasers and servers, which can give a way for which vulnerabilities could also be of concern in defending the community.
After we all know why to trace updates, analysts can decide what info is desired from the monitoring. This weblog submit assumes analysts wish to observe anticipated updates to software program, as a part of managing and safety the community. Figuring out the replace server, whether or not it was polled or downloaded to which consumer or server, and at what time the contact was made to the replace server all present a helpful foundation for this community administration effort. For different functions, alternate info could also be required (e.g., if analysts want to trace the bandwidth consumed by the replace course of, then understanding period and byte quantity of the contacts with the replace server can be vital). The analytic mentioned under is particularly to determine which inner hosts are receiving updates from which supply and over what time interval.
Overview of the Analytic for Monitoring Software program Updates
The analytic coated on this weblog posting assumes that the replace places are identified by the analysts. Widespread URLs for replace places embody:
Analysts could construct a extra site-specific listing by means of dialogue with the community directors as to which replace places are allowed by means of firewalls and different defenses.
The method taken on this analytic is to make use of the listing of replace places and determine transfers of information into the inner community related to these places. The listing of URLs could require conversion by isolating the host portion of it and resolving the IP addresses concerned. These addresses can then be encapsulated as a textual content file, an IP set file, or as an SQL desk, relying on the tooling concerned. The output of this analytic is an inventory of inner addresses and a abstract of the contacts by the replace websites.
A number of totally different instruments can be utilized to trace software program updates. Packet seize and evaluation could possibly be used, however usually the quantity of information and the concentrate on packet element make it time consuming to combination and extract the knowledge to provide the abstract. Intrusion detection system (IDS) guidelines, both for host or network-based IDS, could possibly be established to difficulty an alert every time an replace is made, however such alerts are sometimes onerous to federate throughout a medium or large-size community infrastructure and require filtering and post-processing to supply the abstract info.
Logs, both from purchasers, servers, or safety gadgets, akin to firewalls, may include data of replace contacts. Once more, nonetheless, a time-consuming course of can be wanted to filter, federate, and combination the logs earlier than processing them to determine the abstract info. This weblog describes use of community circulation data (which summarize community connections) and making use of them in a retrospective evaluation (by way of the SiLK instrument suite), streaming evaluation (by way of Evaluation Pipeline), and thru an SQL database.
Implementing the Analytic by way of SiLK
Determine 1 presents a collection of SiLK instructions (SEI’s suite of instruments that retrospectively analyze site visitors expressed as community circulation data) to implement an analytic that tracks software program updates. The rwfilter name isolates site visitors inbound on identified internet ports (80, 8080, or 443) to the monitored community from one of many recognized replace IP addresses, contemplating solely flows representing greater than a protocol handshake (i.e., these with three packets or extra: two for the protocol handshake and not less than one to switch knowledge). The rwuniq name produces a abstract for every vacation spot (inner) tackle displaying the timing of the site visitors. The decision to move abbreviates the output for this weblog and wouldn’t be included for manufacturing use.
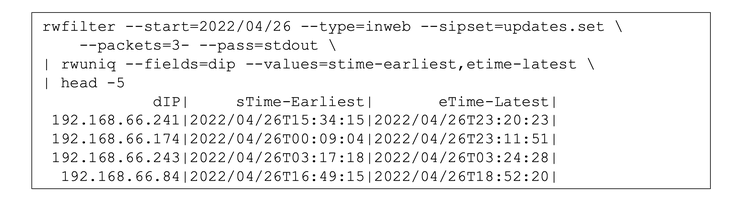
Determine 1: SiLK Instructions and Outcomes
The ends in Determine 1 present 4 inner hosts being contacted (solely 4, as a result of head’s trimming of output). Of those 4, the primary two present contacts over greater than six hours, which is widespread for repeated polling for updates throughout a workday. The latter two present contacts over comparatively transient durations of time (7 minutes and a pair of hours, respectively), which might require extra investigation to find out if these belongings have been solely linked briefly or if the contacts recognized aren’t really replace site visitors. Since this analytic makes use of solely IP tackle and site visitors kind, false positives (i.e., site visitors being labeled as updates when in reality it isn’t) could also be anticipated to happen sometimes. One technique of coping with the false positives can be including an rwfilter name after the preliminary one, which might use a wide range of traits to exclude the falsely recognized data.
Implementing the Analytic by way of Evaluation Pipeline
Determine 2 exhibits the analytic applied as a configuration for Evaluation Pipeline. In distinction to the SiLK model described above, the pipeline analytic identifies replace servers utilizing hostnames, transport protocols, and ports, somewhat than IP addresses. There are separate lists of hostnames for HTTP and HTTPS replace servers. For the reason that hostnames from the replace documentation include wildcards, these lists have to be structured to match the domains, in addition to hosts.
Evaluation Pipeline helps this functionality by including a header line in every listing that flags it as being in DNS format (##format:dns). The primary filter, httpHostDetectUpdate_filter, makes use of the listing for HTTP servers and matches them towards the deep packet inspection (DPI)-derived hostname parsed from the HTTP site visitors, utilizing the prolonged circulation fields which can be populated by YAF. This filter solely considers (1) data from one of many servers to the monitored community’s inner addresses and (2) site visitors to the widespread internet transport port (TCP/80) with three packets or extra (once more, excluding site visitors consisting solely of protocol overhead).
The second filter, sslServerDetectUpdate_filter, follows an identical course of however makes use of the sslServerName matched towards the HTTPS server listing and the HTTPS widespread port (TCP/443). The output of those two filters is mixed within the third filter, updateDetect_filter, which in flip is invoked by the inner filter, updateDetect_intfilter, to assemble a day by day listing of addresses on the monitored community which have contacts from the replace servers. This listing is reported to a file by the listing configuration, updateDetect_list. Evaluation Pipeline produces solely this set file as an output, so no show is proven in Determine 2.

Determine 2: Evaluation pipeline configuration for Analytic
Implementing the Analytic by way of SQL
Determine 3 offers an implementation of the analytic in SQL-like notation. This notional instance assumes that IPFIX (an Web-standard circulation report format described in RFC7011) info parts are current in a desk of data, known as flowData, and that the listing of identified replace hosts is current in a separate desk known as updateTable and having IP tackle and port info in that desk. The inside SELECT isolates related info parts for data the place the supply tackle matches an replace server, and the port and protocol additionally match, contemplating solely data for flows aggregating greater than three packets. The outer SELECT assertion produces a abstract just like the output of the SiLK analytic in Determine 1.
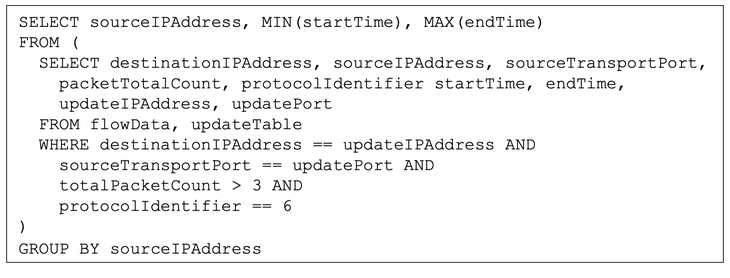
Determine 3: Notional SQL implementation of Analytic
Understanding Software program Adjustments
Whichever type of tooling is used, analysts usually want an understanding of the software program adjustments to their networks, even the anticipated ones. The analytic introduced on this weblog posting offers a primary step at this understanding, though over time analysts ought to revise and specialize it to replicate their wants. A number of of the next potential causes may have additional investigation if the noticed updates lack most of the anticipated ones:
- There was a change within the replace servers, and the listing utilized in monitoring have to be up to date. (Trace: see if different inner belongings are being up to date from the server in query)
- There was a change within the inner host: both taken out of service or had its software program reconfigured. (Trace: see what different exercise is current for the inner host)
- The inner host’s administrator or an attacker has disabled the replace service, which is normally opposite to safety coverage. (Trace: contact the approved administrator for the inner host)
- There’s a community connectivity difficulty with respect to the inner host or the replace server. (Trace: validate the connectivity concerned)
- Different components have interfered with the replace course of.
The impression of those causes on the community safety will fluctuate relying on the vary of belongings affected and the criticality of these belongings, however a few of the causes could demand instant response.