In a seamless signal that menace actors are adapting nicely to a post-macro world, it has emerged that using Microsoft OneNote paperwork to ship malware through phishing assaults is on the rise.
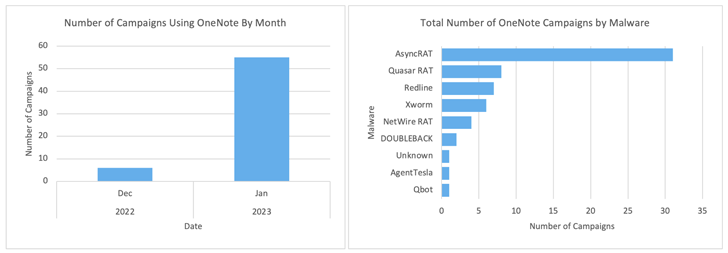
A few of the notable malware households which are being distributed utilizing this methodology embody AsyncRAT, RedLine Stealer, Agent Tesla, DOUBLEBACK, Quasar RAT, XWorm, Qakbot, BATLOADER, and FormBook.
Enterprise agency Proofpoint mentioned it detected over 50 campaigns leveraging OneNote attachments within the month of January 2023 alone.
In some situations, the e-mail phishing lures comprise a OneNote file, which, in flip, embeds an HTA file that invokes a PowerShell script to retrieve a malicious binary from a distant server.
Different eventualities entail the execution of a rogue VBScript that is embedded throughout the OneNote doc and hid behind a picture that seems as a seemingly innocent button. The VBScript, for its half, is designed to drop a PowerShell script to run DOUBLEBACK.
“You will need to be aware, an assault is barely profitable if the recipient engages with the attachment, particularly by clicking on the embedded file and ignoring the warning message displayed by OneNote,” Proofpoint mentioned.
The an infection chains are made attainable owing to a OneNote function that enables for the execution of choose file sorts immediately from throughout the note-taking utility in what’s a case of a “payload smuggling” assault.
“Most file sorts that may be processed by MSHTA, WSCRIPT, and CSCRIPT may be executed from inside OneNote,” TrustedSec researcher Scott Nusbaum mentioned. “These file sorts embody CHM, HTA, JS, WSF, and VBS.”
As remedial actions, Finnish cybersecurity agency WithSecure is recommending customers block OneNote mail attachments (.one and .onepkg information) and maintain shut tabs on the operations of the OneNote.exe course of.
The shift to OneNote is seen as a response to Microsoft’s determination to disallow macros by default in Microsoft Workplace functions downloaded from the web final yr, prompting menace actors to experiment with unusual file sorts akin to ISO, VHD, SVG, CHM, RAR, HTML, and LNK.
The purpose behind blocking macros is two-fold: To not solely scale back the assault floor but in addition improve the trouble required to tug off an assault, at the same time as e-mail continues to be the high supply vector for malware.
However these are usually not the one choices which have develop into a well-liked approach to conceal malicious code. Microsoft Excel add-in (XLL) information and Writer macros have additionally been put to make use of as an assault pathway to skirt Microsoft’s protections and propagate a distant entry trojan referred to as Ekipa RAT and different backdoors.
The abuse of XLL information hasn’t gone unnoticed by the Home windows maker, which is planning an replace to “block XLL add-ins coming from the web,” citing an “growing variety of malware assaults in current months.” The choice is predicted to be out there someday in March 2023.
When reached for remark, Microsoft advised The Hacker Information that it had nothing additional to share presently.
“It is clear to see how cybercriminals leverage new assault vectors or less-detected means to compromise consumer units,” Bitdefender’s Adrian Miron mentioned. “These campaigns are prone to proliferate in coming months, with cybercrooks testing out higher or improved angles to compromise victims.”