Authored by Dexter Shin
McAfee’s Cellular Analysis Crew has recognized new malware on the Google Play Retailer. Most of them are disguising themselves as cleaner apps that delete junk recordsdata or assist optimize their batteries for gadget administration. Nonetheless, this malware hides and constantly present commercials to victims. As well as, they run malicious providers mechanically upon set up with out executing the app.
HiddenAds features and promotion
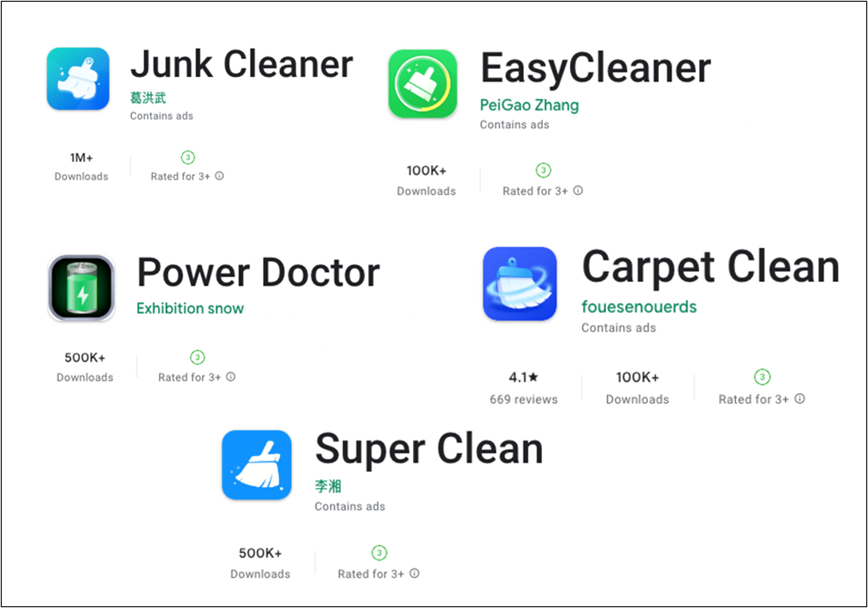
They exist on Google Play though they’ve malicious actions, so the sufferer can seek for the next apps to optimize their gadget.
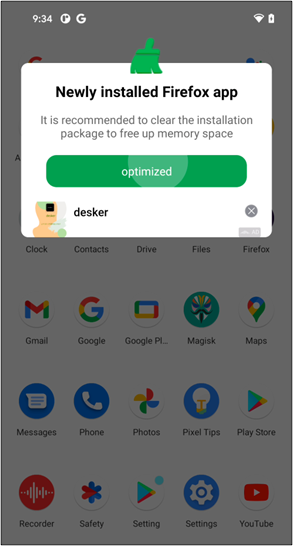
Customers could usually assume putting in the app with out executing it’s protected. However you’ll have to alter your thoughts due to this malware. Once you set up this malware in your gadget, it’s executed with out interplay and executes a malicious service.
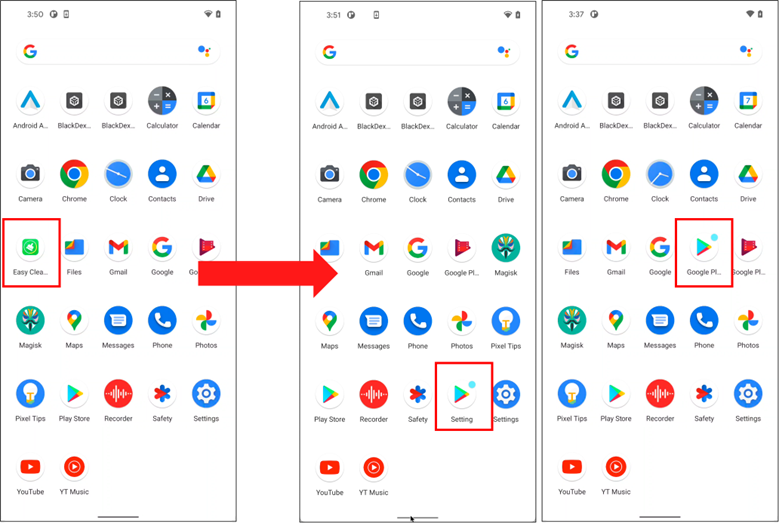
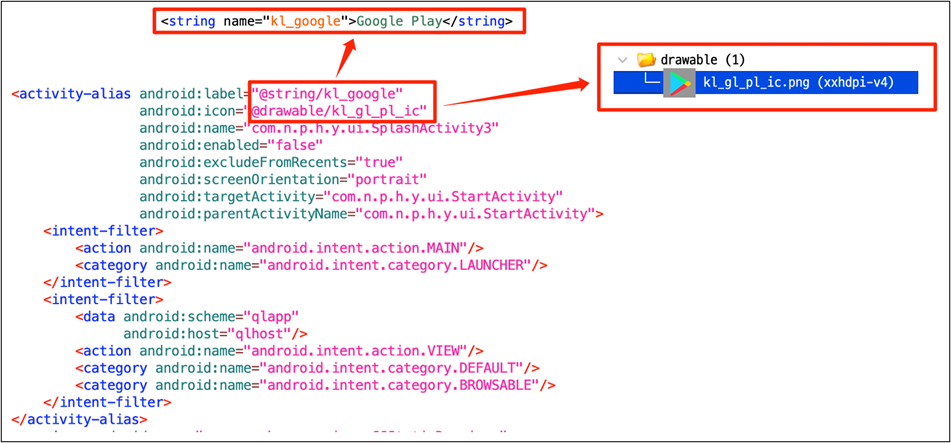
As well as, they attempt to cover themselves to forestall customers from noticing and deleting apps. Change their icon to a Google Play icon that customers are conversant in and alter its identify to ‘Google Play’ or ‘Setting.’
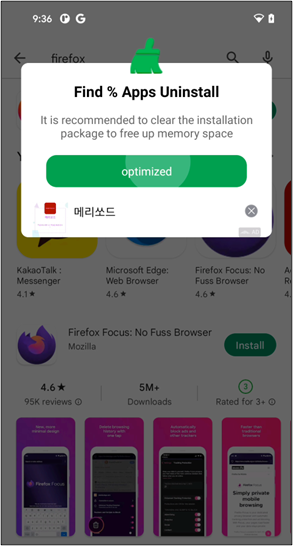
Robotically executed providers consistently show commercials to victims in a wide range of methods.
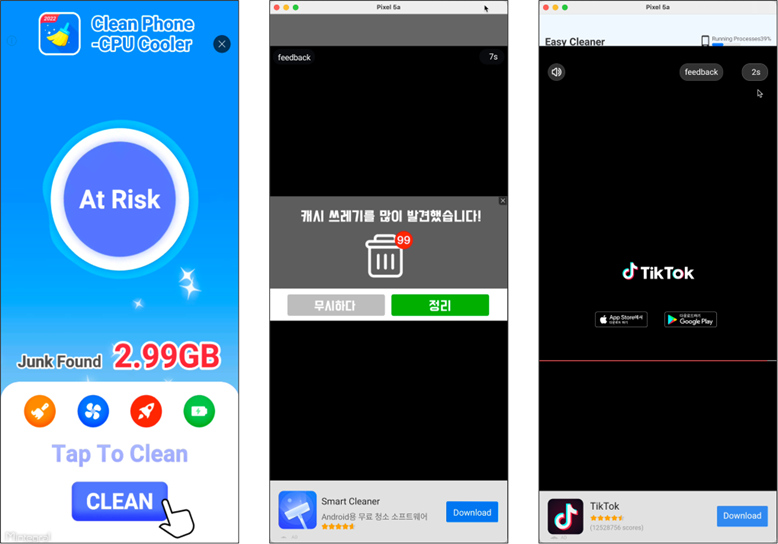
These providers additionally induce customers to run an app once they set up, uninstall, or replace apps on their units.
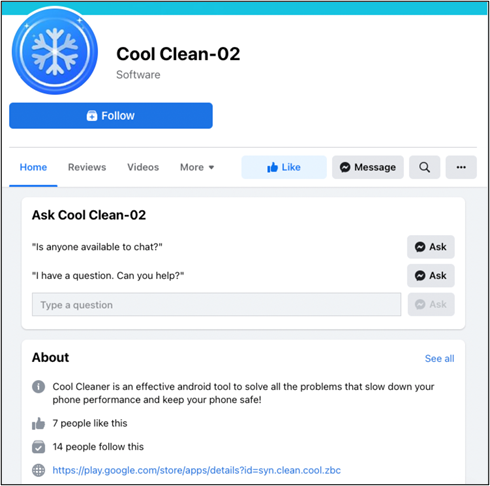
To advertise these apps to new customers, the malware authors created promoting pages on Fb. As a result of it’s the hyperlink to Google Play distributed via respectable social media, customers will obtain it definitely.


The way it works
This malware makes use of the Contact Supplier. The Contact Supplier is the supply of information you see within the gadget’s contacts software, and you may as well entry its information in your individual software and switch information between the gadget and on-line providers. For this, Google offers ContactsContract class. ContactsContract is the contract between the Contacts Supplier and purposes. In ContactsContract, there’s a class known as Listing. A Listing represents a contacts corpus and is carried out as a Content material Supplier with its distinctive authority. So, builders can use it in the event that they wish to implement a customized listing. The Contact Supplier can acknowledge that the app is utilizing a customized listing by checking particular metadata within the manifest file.
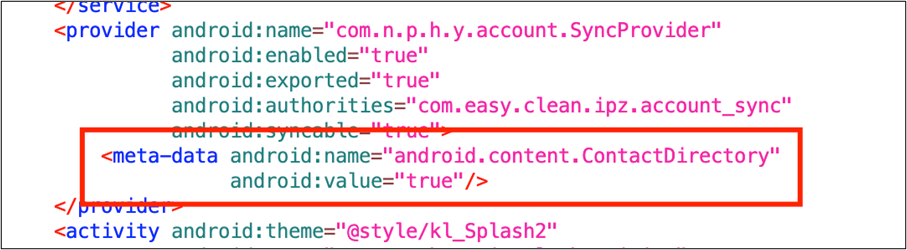
The necessary factor is the Contact Supplier mechanically interrogates newly put in or changed packages. Thus, putting in a bundle containing particular metadata will all the time name the Contact Supplier mechanically.
The primary exercise outlined within the software tag within the manifest file is executed as quickly as you put in it simply by declaring the metadata. The primary exercise of this malware will create a everlasting malicious service for displaying commercials.
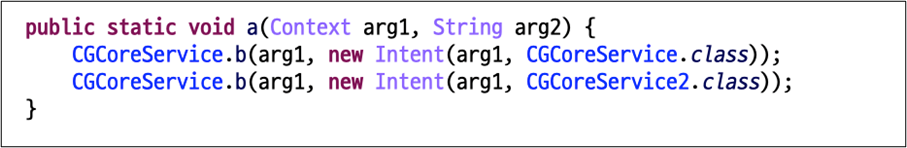
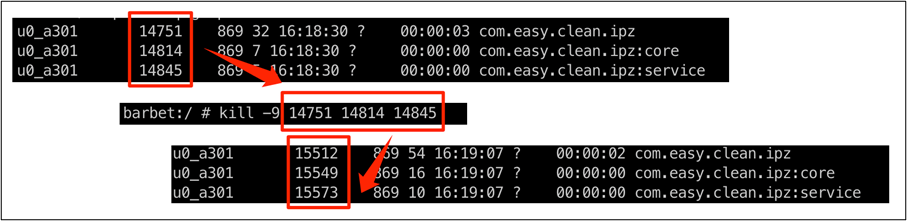
As well as, the service course of will generate instantly even whether it is pressured to kill.
Subsequent, they alter their icons and names utilizing the <activity-alias> tag to cover.
Customers contaminated worldwide
It’s confirmed that customers have already put in these apps from 100K to 1M+. Contemplating that the malware works when it’s put in, the put in quantity is mirrored because the sufferer’s quantity. In line with McAfee telemetry information, this malware and its variants have an effect on a variety of nations, together with South Korea, Japan, and Brazil:

Conclusion
This malware is auto-starting malware, in order quickly because the customers obtain it from Google Play, they’re contaminated instantly. And it’s nonetheless consistently growing variants which can be printed by completely different developer accounts. Due to this fact, it isn’t simple for customers to note any such malware.
We already disclosed this risk to Google and all reported purposes had been faraway from the Play Retailer. Additionally, McAfee Cellular Safety detects this risk as Android/HiddenAds and protects you from any such malware. For extra details about McAfee Cellular Safety, go to https://www.mcafeemobilesecurity.com
Indicators of Compromise
Purposes:
| App Identify | Bundle Identify | Downloads |
| Junk Cleaner | cn.junk.clear.plp | 1M+ |
| EasyCleaner | com.simple.clear.ipz | 100K+ |
| Energy Physician | com.energy.physician.mnb | 500K+ |
| Tremendous Clear | com.tremendous.clear.zaz | 500K+ |
| Full Clear -Clear Cache | org.stemp.fll.clear | 1M+ |
| Fingertip Cleaner | com.fingertip.clear.cvb | 500K+ |
| Fast Cleaner | org.qck.cle.oyo | 1M+ |
| Hold Clear | org.clear.sys.lunch | 1M+ |
| Windy Clear | in.cellphone.clear.www | 500K+ |
| Carpet Clear | og.crp.cln.zda | 100K+ |
| Cool Clear | syn.clear.cool.zbc | 500K+ |
| Sturdy Clear | in.reminiscence.sys.clear | 500K+ |
| Meteor Clear | org.ssl.wind.clear | 100K+ |
SHA256:
- 4b9a5de6f8d919a6c534bc8595826b9948e555b12bc0e12bbcf0099069e7df90
- 4d8472f0f60d433ffa8e90cc42f642dcb6509166cfff94472a3c1d7dcc814227
- 5ca2004cfd2b3080ac4958185323573a391dafa75f77246a00f7d0f3b42a4ca3
- 5f54177a293f9678797e831e76fd0336b0c3a4154dd0b2175f46c5a6f5782e24
- 7a502695e1cab885aee1a452cd29ce67bb1a92b37eed53d4f2f77de0ab93df9b
- 64d8bd033b4fc7e4f7fd747b2e35bce83527aa5d6396aab49c37f1ac238af4bd
- 97bd1c98ddf5b59a765ba662d72e933baab0a3310c4cdbc50791a9fe9881c775
- 268a98f359f2d56497be63a31b172bfbdc599316fb7dec086a937765af42176f
- 690d658acb9022765e1cf034306a1547847ca4adc0d48ac8a9bbdf1e6351c0f7
- 75259246f2b9f2d5b1da9e35cab254f71d82169809e5793ee9c0523f6fc19e4b
- a5cbead4c9868f83dd9b4dc49ca6baedffc841772e081a4334efc005d3a87314
- c75f99732d4e4a3ec8c19674e99d14722d8909c82830cd5ad399ce6695856666
Domains:
- http[://]hw.sdk.functionads.com:8100






