Microsoft on Thursday flagged a cross-platform botnet that is primarily designed to launch distributed denial-of-service (DDoS) assaults in opposition to non-public Minecraft servers.
Known as MCCrash, the botnet is characterised by a novel spreading mechanism that enables it to propagate to Linux-based gadgets regardless of originating from malicious software program downloads on Home windows hosts.
“The botnet spreads by enumerating default credentials on internet-exposed Safe Shell (SSH)-enabled gadgets,” the corporate stated in a report. “As a result of IoT gadgets are generally enabled for distant configuration with probably insecure settings, these gadgets might be in danger to assaults like this botnet.”
This additionally implies that the malware may persist on IoT gadgets even after eradicating it from the contaminated supply PC. The tech large’s cybersecurity division is monitoring the exercise cluster beneath its rising moniker DEV-1028.
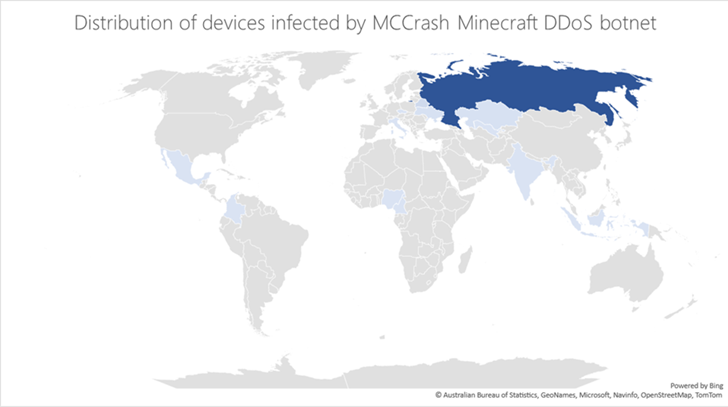
A majority of the infections have been reported in Russia, and to a lesser extent in Kazakhstan, Uzbekistan, Ukraine, Belarus, Czechia, Italy, India, Indonesia, Nigeria, Cameroon, Mexico, and Columbia. The corporate didn’t disclose the precise scale of the marketing campaign.
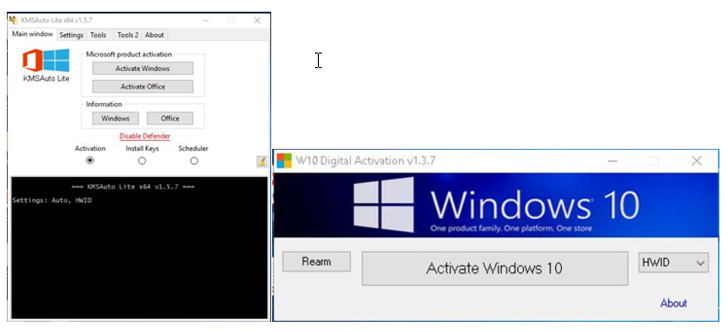
The preliminary an infection level for the botnet is a pool of machines which have been compromised by way of the set up of cracking instruments that declare to offer unlawful Home windows licenses.
The software program subsequently acts as a conduit to execute a Python payload that incorporates the core options of the botnet, together with scanning for SSH-enabled Linux gadgets to launch a dictionary assault.
Upon breaching a Linux host utilizing the propagation methodology, the identical Python payload is deployed to run DDoS instructions, one among which is particularly set as much as crash Minecraft servers (“ATTACK_MCCRASH”).
Microsoft described the strategy as “extremely environment friendly,” noting it is seemingly provided as a service on underground boards.
“Such a menace stresses the significance of making certain that organizations handle, preserve updated, and monitor not simply conventional endpoints but additionally IoT gadgets which are usually much less safe,” researchers David Atch, Maayan Shaul, Mae Dotan, Yuval Gordon, and Ross Bevington stated.
The findings come days after Fortinet FortiGuard Labs revealed particulars of a brand new botnet dubbed GoTrim, which has been noticed brute-forcing self-hosted WordPress web sites.