Essential infrastructure is essential for societal existence, progress, and growth. Societies are reliant on the providers supplied by vital infrastructure sectors like telecommunication, vitality, healthcare, transportation, and data know-how. Security and safety are needed for the optimum operation of those vital infrastructures. Essential infrastructure is made up of digital and non-digital belongings. Organizations should keep forward of cybersecurity threats to forestall failures attributable to cyber assaults on vital infrastructure. Discovering methods to guard digital belongings in an ever-changing panorama full of threats is a steady exercise. Organizations should additionally make use of environment friendly safety options and greatest practices to remain protected and cut back the probabilities of compromise.
Safety options assist safe and enhance the visibility of a company’s menace panorama. Completely different options use completely different ideas and approaches. An essential idea that has risen not too long ago is Prolonged Detection and Response (XDR).
XDR options present detection and response capabilities throughout a number of layers. XDR instruments correlate knowledge utilizing menace detection and response strategies by gathering logs and occasions from varied sources, resembling community gadgets, servers, and functions. These capabilities make it attainable for safety groups to shortly detect, examine and reply to incidents.
Assaults on vital infrastructure
In February 2022, a provide chain assault occurred in one among Germany’s vitality giants. This assault led to the closure of greater than 200 gasoline stations throughout Germany, affecting lives and companies. This occasion occurred practically a yr after the Colonial Pipeline assault in the US of America, the place knowledge exfiltration occurred and a ransomware an infection shut down digital providers inside their infrastructure for days. An article from the NYTimes reported that an estimated 5 million {dollars} have been paid to the hackers concerned within the Colonial Pipeline ransomware assault. The hackers within the Colonial Pipeline case have been in a position to achieve entry utilizing a compromised VPN password, they usually proceeded to carry out intrusion actions for a whole day earlier than they have been detected.
There are a number of entry factors for assaults on vital infrastructure, and a few vectors are extra prevalent than others. These vectors embrace compromised credentials, unpatched working methods, weak functions, and malware delivered by varied strategies.
Emphasis must be positioned on securing vital infrastructure earlier than an assault occurs, no matter the way it originates. Safety options assist organizations shield themselves from completely different assault vectors. These options embrace XDR, SIEM, code scanners, infrastructure analyzers, vulnerability scanners, and malware detection options. Along with these options are compliance requirements. A couple of advisable requirements are NIST, PCI DSS, HIPAA, and GDPR. The proper utility of those options and compliance requirements may help enhance a company’s safety posture.
How XDR can mitigate assaults
An XDR performs a big function in conditions the place menace actors goal completely different digital belongings of a company. With an XDR built-in into a company’s infrastructure, safety occasions from varied sources and belongings are analyzed and correlated to find out what actions are taking place within the infrastructure. An XDR has the power to detect and supply automated responses to malicious actions in an surroundings. Such a response can kill a malicious course of, delete a malicious file, or isolate a compromised endpoint. Because the responses are executed in close to real-time, pace performs a vital function within the execution of those duties.
Wazuh SIEM/XDR
Wazuh is a free and open supply SIEM and XDR platform. It contains a number of parts that shield each cloud and on-premises workloads. The Wazuh platform operates with an agent-server mannequin. The Wazuh central parts (server, indexer, and dashboard) analyze safety knowledge from endpoints in your infrastructure. On the identical time, the Wazuh agent is deployed on endpoints to gather safety knowledge and supply menace detection and response. The Wazuh agent is light-weight and helps a number of platforms. Wazuh additionally helps agentless monitoring on routers, firewalls, and switches.
Wazuh XDR capabilities
Wazuh has a number of capabilities that assist a company keep forward of safety threats. A few of these capabilities are malware detection, vulnerability detection, file integrity monitoring, and automatic response to threats, amongst others. The next sections comprise extra particulars on Wazuh capabilities that assist in defending vital infrastructure.
Log knowledge evaluation
The Wazuh log knowledge evaluation module collects and analyzes safety knowledge from varied sources. Such knowledge embrace system occasion logs, utility logs, and irregular system habits logs. Consequently, the analyzed knowledge is used for menace detection and automatic response. This functionality provides you visibility into occasions taking place at completely different endpoints in your infrastructure.
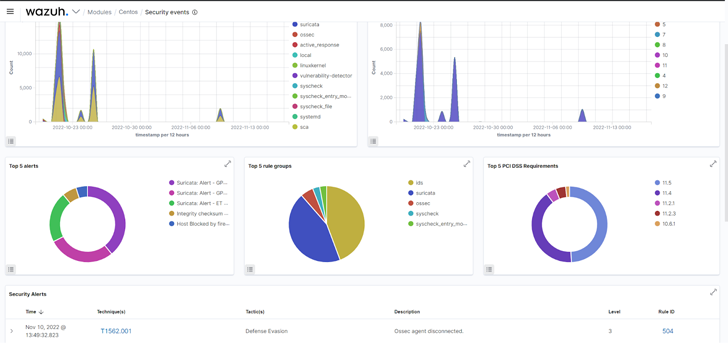 |
| Fig 1: Safety occasions of a monitored endpoint on the Wazuh dashboard. |
Malware detection
Wazuh has a number of options that assist in malware detection. As well as, Wazuh might be built-in with different safety instruments like YARA and VirusTotal to detect malware. By correctly configuring Wazuh Fixed Database (CDB) lists, values from decoded alerts resembling customers, file hashes, IP addresses, or domains might be in contrast with malicious data. Here’s a weblog publish that reveals how Wazuh might be built-in with CDB lists for detecting and responding to malicious recordsdata. This Wazuh functionality helps you detect malware on varied monitored endpoints.
File integrity monitoring
The Wazuh File Integrity Monitoring (FIM) module screens an endpoint filesystem to detect modifications in predefined recordsdata and directories. Alerts are triggered when a file is created, modified, or deleted in monitored directories. You possibly can see how this module is utilized to detect modifications to an SSH key file within the weblog publish Detecting illegitimate crypto miners on Linux endpoints. Utilizing the Wazuh FIM module, you possibly can detect modifications to configuration recordsdata on vital methods and decide if the exercise is permitted or malicious.
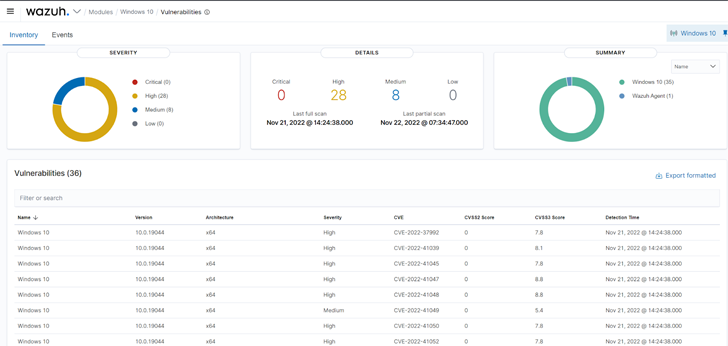
Vulnerability detection
Wazuh makes use of the Vulnerability detector module to search out vulnerabilities on a monitored endpoint. Vulnerability detection works by performing software program audits. These audits are made attainable by leveraging vulnerability feeds listed from sources like Canonical, Debian, Crimson Hat, Arch Linux, ALAS (Amazon Linux Advisories Safety), Microsoft, and the Nationwide Vulnerability Database. These feeds are cross-correlated by Wazuh with info from the endpoint’s utility stock. Directors ought to start remediation instantly after vulnerabilities are detected earlier than malicious actors can exploit them.
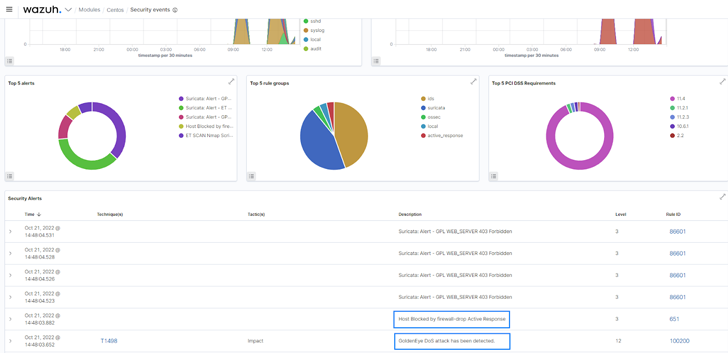
Automated response to threats
The Wazuh lively response module might be configured to mechanically execute countermeasures when occasions match particular standards. It could execute user-defined actions, resembling a firewall block or drop, site visitors shaping or throttling, account lockout, system shutdown, and so forth. The lively response module was configured to disclaim community connection from an recognized malicious supply within the weblog publish Responding to community assaults with Suricata and Wazuh XDR.
Conclusion
Implementing safety throughout a number of layers of vital infrastructure reduces a company’s assault floor. We now have emphasised a couple of components to remember to keep up a correct safety posture. In defending your digital belongings, we propose an answer that works properly with varied endpoints, methods, and applied sciences.
Wazuh is a free and open supply XDR resolution. It contains the capabilities needed to find vulnerabilities, decide the system configuration state, and reply to threats in your digital belongings. Wazuh additionally supplies help for compliance requirements like PCI DSS, HIPAA, NIST, and GDPR. Wazuh has an ever-growing neighborhood the place help is supplied to customers. Try the Wazuh documentation for extra info.