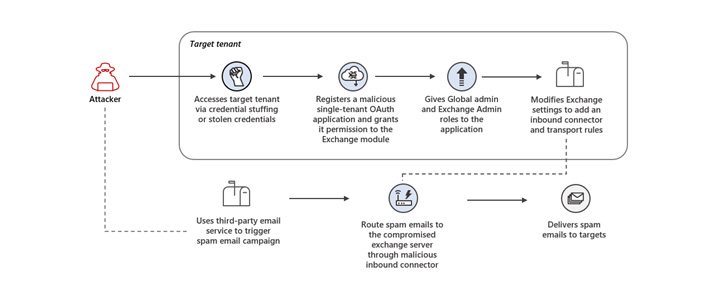
Microsoft on Thursday warned of a consumer-facing assault that made use of rogue OAuth purposes deployed on compromised cloud tenants to finally seize management of Alternate servers and unfold spam.
“The menace actor launched credential stuffing assaults towards high-risk accounts that did not have multi-factor authentication (MFA) enabled and leveraged the unsecured administrator accounts to realize preliminary entry,” the Microsoft 365 Defender Analysis Group stated.
The unauthorized entry to the cloud tenant permitted the adversary to register a malicious OAuth utility and grant it elevated permissions, and ultimately modify Alternate Server settings to permit inbound emails from particular IP addresses to be routed by means of the compromised e mail server.
“These modifications to the Alternate server settings allowed the menace actor to carry out their major purpose within the assault: sending out spam emails,” Microsoft stated. “The spam emails have been despatched as a part of a misleading sweepstakes scheme meant to trick recipients into signing up for recurring paid subscriptions.”
The e-mail messages urged the recipients to click on on a hyperlink to obtain a prize, doing so which redirected the victims to a touchdown web page that requested the victims to enter their bank card particulars for a small transport price to gather the reward.
The menace actor additional carried out a variety of steps to evade detection and proceed its operations for prolonged durations of time, together with taking weeks and even months to make use of the malicious OAuth utility after it was arrange and deleting the modifications made to the Alternate Server after every spam marketing campaign.
Microsoft’s menace intelligence division stated that the adversary has been actively working spam e mail campaigns for a number of years, usually sending excessive volumes of spam emails briefly bursts by means of a wide range of strategies.
Though the first purpose of the assault seems to be to trick unwitting customers into signing up for undesirable subscription providers, it might have posed a much more critical menace had the identical approach been used to steal credentials or distribute malware.
“Whereas the follow-on spam marketing campaign targets client e mail accounts, this assault targets enterprise tenants to make use of as infrastructure for this marketing campaign,” Microsoft stated. “This assault thus exposes safety weaknesses that might be utilized by different menace actors in assaults that would instantly influence affected enterprises.”