In 2020, the United Nations estimated the full inhabitants of Africa at 1.3 billion, with 60 p.c of the inhabitants below the age of 24. On the identical time, the inhabitants continues to embrace, in ever-increasing numbers, the usage of the Web and different internet applied sciences. With this development in nations that always lack the required infrastructure and experience comes the inevitable improve in cybersecurity incidents and knowledge breaches. As authorities leaders work to create a secure and intensive expertise infrastructure, they have to additionally work to offer alternatives for important coaching and expertise acquisition for present and future African authorities workers, professionals, and college students. The mere existence of quick Web and overseas investments just isn’t ample. As an alternative the main target is on the creation of expert cybersecurity human capital that can work with present applied sciences and develop new innovation to resolve real-life threats distinctive to the African continent. This weblog put up, which is tailored and excerpted from a lately printed paper that I coauthored with Michelle Ramin, explores points surrounding cybersecurity capability constructing with human capital in Africa.
What Is Capability Constructing of Human Capital?
Capability constructing of human capital is outlined because the strategic improvement of teaching, coaching, and mentoring of cybersecurity personnel. It’s a continuous studying course of wherein cybersecurity personnel conduct workouts in real-life situations and have interaction in data switch, proficiency enchancment, functionality improvement, and expertise constructing throughout ranges of complexity.
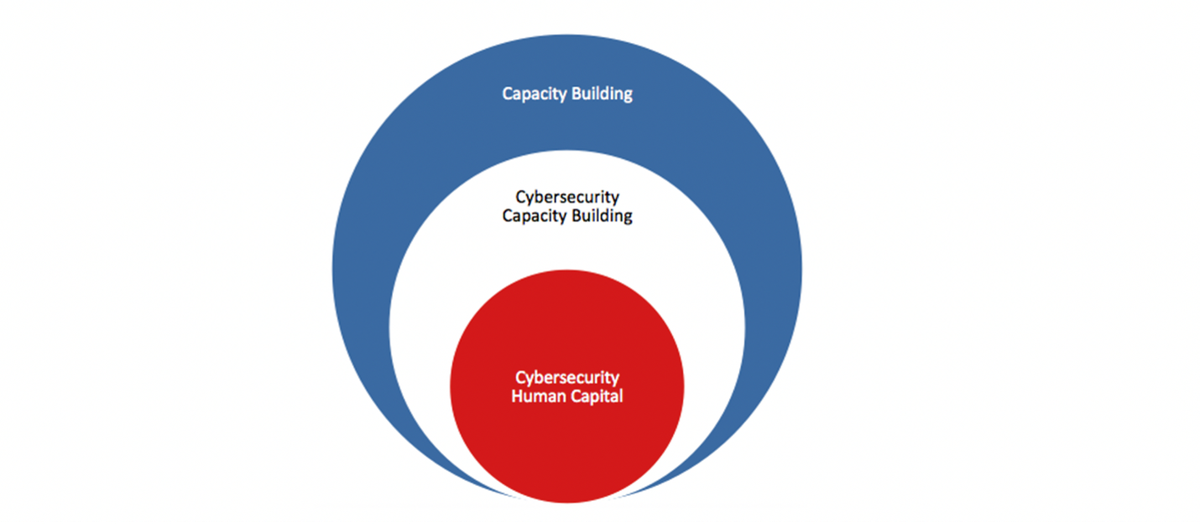
This definition emphasizes the function of stakeholders, together with authorities, personal sector, educational establishments, faculties, and people. Capability constructing of human capital is thus a important part of cybersecurity capability constructing. “Human capital” refers back to the human sources, their understanding, data, expertise, and capabilities to carry out. Determine 1 depicts the connection among the many varied parts famous above.

Cybersecurity Capability Constructing in Africa and U.S. Authorities Partnership
Efforts on behalf of the US to increase capability constructing in Africa have been ongoing. Many African nations lack monetary sources, Web infrastructure, and homegrown cybersecurity experience. In 2014, 54 African nations making up the African Union (AU) adopted the Conference on Cyber Safety and Private Information Safety (often known as the Malabo Conference) with the purpose of securing digital transactions, defending private knowledge, and deterring cybersecurity and cybercrime.
As time progressed, solely a handful of nations endorsed the Malabo Conference and adopted a proper coverage, leading to a weak alliance and implementation. Many nations seemed to be working independently and thus have been sluggish to undertake and cling to a regional cybersecurity technique. Actually, below the steering of the U.S. Division of State’s Workplace of the Coordinator for Cyber Points, in Africa eight nations have created nationwide cybersecurity methods, and 13 nations have organized nationwide laptop emergency response groups.
Such a cybersecurity digital divide has a far-reaching impact on the area’s financial productiveness, in addition to the flexibility of state governments and native enterprise organizations to rent native cybersecurity human capital. The AU has lengthy advocated for the collaboration and sharing of secure expertise and Web infrastructures amongst members due to the excessive value of funding. Adopting such an method, nonetheless, requires establishing belief amongst AU members as a part of long-term collaborative efforts.
In the US, a number of consortia allow useful resource sharing. For instance, the Division of Homeland Safety (DHS) Cybersecurity Info Sharing and Collaboration Program (CISCP) allows the change of unclassified actionable, related, and well timed info amongst stakeholders via trusted private and non-private partnerships throughout important infrastructure (CI) sectors. The CISCP program helps stakeholders handle cyber dangers via analyst-to-analyst sharing of utilized risk and vulnerability info, comparable to indicator bulletins, evaluation studies, joint-analysis studies, malware-findings studies, malware-analysis studies, and joint-indicator bulletins. This info shared amongst CISCP stakeholders is ruled utilizing the Visitors Mild Protocol (TLP), permitting the submitter to regulate the dealing with, classification, and sharing/dissemination of their info.
One other US-based cyber info sharing mannequin is the Info Sharing and Evaluation Middle (ISAC) mannequin. The ISAC relies on a hub-and-spoke structure, the place the central hub receives info from taking part members (the spokes). On this structure the hub can both redistribute the data acquired to its members or present value-added providers, augmenting the information in an effort to make it extra helpful and related to members.
To implement information-sharing mechanisms, many African nations are following these U.S. requirements. Furthermore, the State Division is stepping up its efforts to inspire and promote a holistic government-to-government method to increase the cybersecurity capability constructing within the area. As famous earlier, the cyber expertise hole can also be relevant to present workers. Most of the time, the query {that a} safety analyst can have is, “Now that I’ve these instruments, what do I do with them?”
Enhancing cybersecurity capability constructing enhances the flexibility of nationwide governments to create CSIRTs to grasp and reply to real-time cyber threats via info sharing, incident response coordination, and mitigation collaboration. The Cybersecurity Infrastructure Safety Company defines a CSIRT as
a concrete organizational entity (i.e., a number of employees) that’s assigned the accountability for coordinating and supporting the response to a pc safety occasion or incident. CSIRTs may be created for nation states or economies, governments, business organizations, instructional establishments, and even non-profit entities. The purpose of a CSIRT is to attenuate and management the injury ensuing from incidents, present efficient steering for response and restoration actions, and work to forestall future incidents from taking place
As I wrote in my 2017 put up, nationwide CSIRTs have taken a distinguished function as factors of contact within the coordination and response to nationwide, regional, and worldwide computer-security incidents. Earlier and present administrations have set forth cybersecurity insurance policies that allow the US to pursue worldwide cooperation in sustaining a globally safe and resilient Web with accomplice and ally nations. In 2014 the SEI CERT Division and the U.S. Division of State Workplace of the Coordinator for Cyber Points (S/CCI), in coordination with the Division of Homeland Safety Workplace of Worldwide Affairs, started creating and implementing world cybersecurity capacity-building actions that assist functionality and capability constructing for national-level CSIRTs.
To find out the capability wherein a CSIRT operates, the SEI has developed the CSIRT Growth Capability Continuum. The continuum illustrates a CSIRT’s capabilities on a scale from 0 (a nascent CSIRT) to five (the place the CSIRT is described as being on the “vanguard and progressive”). To categorise a CSIRT inside this continuum, a sequence of interviews are performed with the nationwide CSIRTs of the partnering nations. These interviews are throughout the scope of the SEI Nationwide CSIRT Growth Mentoring Framework, which is utilized in 4 linear phases, as proven in Determine 2 and described under.
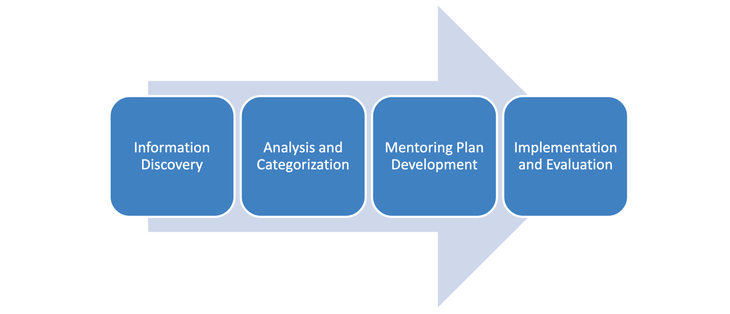
Part 1: Info Discovery. This section helps the mentor crew perceive the group requiring mentoring and decide the feasibility for offering help. The data gathered right here is the inspiration for all the opposite parts on which the framework is constructed. The primary actions on this section embody the next:
- Establish the help that the CSIRT needs.
- Submit an information-gathering survey to the CSIRT for completion.
- Carry out a public-source literature overview.
- Acquire perception concerning the CSIRT from put up (the U.S. embassy within the nation).
- Acquire perception from accomplice CSIRTs.
- Interview CSIRT members and constituents.
- Conduct an onsite go to with the CSIRT.
- Acquire insights from authorities or business stakeholders within the nation.
- Establish earlier coaching or mentoring acquired by the CSIRT.
- Carry out a nationwide CSIRT evaluation as a part of the onsite go to (elective).
Part 2: Evaluation and Categorization. On this section, knowledge collected through the Info Discovery section is analyzed and used to find out the present capability of the mentee CSIRT, and a plan of motion is beneficial to assist enhance the CSIRT’s functionality, together with the next actions:
- Establish the CSIRT’s mission, objectives, and scope.
- Establish present CSIRT actions, providers, and operations.
- Establish CSIRT wants primarily based on the help desired.
- Establish particular circumstances.
- Benchmark the CSIRT in opposition to the CSIRT Capability Growth Continuum.
- Establish the CSIRT’s capability stage.
- Carry out a spot evaluation.
- Establish mentoring necessities.
- Establish potential mentors or companions.
Part 3: Mentoring Plan Growth. Throughout this section, actions collectively agreed on by the mentor and mentee are developed and documented. This course of contains attainable mentoring choices, mentoring methods and actions primarily based on necessities, and the creation of a corresponding roadmap, plan of motion, and milestones. It additionally contains socializing the plan with the mentee and its stakeholders. The primary actions on this section embody the next:
- Establish related mentoring/help choices.
- Select mentoring methods and actions.
- Create the mentoring plan and roadmap.
- Socialize and acquire settlement on the mentoring plan.
- Create a mentoring venture plan and milestones.
Part 4: Implementation and Analysis. The ultimate section entails implementing particular mentoring duties outlined within the mentoring and coaching plan, monitoring the progress of the plan, and evaluating the success of the executed plan utilizing an evaluation methodology. As soon as the mentoring engagement is full, the mentoring crew may match with the framework maintainer to find out acceptable subsequent steps primarily based on what has been discovered.
The primary actions on this section embody the next:
- Implement the mentoring and coaching plan and roadmap.
- Observe milestones and accomplishments.
- Collect suggestions.
- Regulate plans as wanted.
- Carry out a postmortem.
- Assess success.
- Collect classes discovered for inclusion within the mentoring framework.
- Doc the method as a part of the organizational data.
Establishing Cybersecurity Human Capital
As we acknowledged earlier within the put up U.S. State Division has labored with a number of African nations to ascertain cybersecurity human-capital capability constructing. Furthermore, a collaborative effort is ongoing because the taking part nations proceed to work on creating superior phases of cybersecurity human-capital expertise constructing.
The rest of this put up explores the significance of capability constructing of human capital, which is a important part of cybersecurity capability constructing, as mentioned above. The institution of cybersecurity human capital entails a number of steps, starting with the event and implementation of cybersecurity consciousness applications.
A authorities company will carry out consciousness campaigns, together with slogans, posters, pamphlets, and so forth., collaboratively with stakeholders in the neighborhood (e.g., college students, enterprise organizations, authorities companies). Different consciousness actions embody the creation of an annual Cybersecurity Month and the institution of an internet presence and social media campaigns. Furthermore, consciousness campaigns ought to be created for enterprise leaders and executives in key industries, comparable to banking, retail, training, and healthcare, to teach them concerning the dangers and threats of their organizations.
One instance of a profitable marketing campaign developed by the U.S. Division of Homeland Safety is the creation of the slogan STOP.THINK.CONNECT. This slogan highlights to finish customers the dangers that include being on-line. This profitable marketing campaign has been prolonged internationally.
The second step in establishing cybersecurity human capital entails the event of education schemes in main, secondary, and post-secondary faculties. As expertise evolves, so does the cybersecurity panorama. To stay related, education schemes ought to observe the lead supplied by business and sustain with altering applied sciences.
In a 2016 report titled The Evolution of Safety Expertise by IT certification authority CompTIA, 350 organizations have been surveyed concerning the ability units that have been thought-about essential on safety groups. The highest two expertise recognized have been community/infrastructure safety and data of varied threats, as proven within the graphic under. Each of those ability units require that people not solely acquire an understanding of core ideas, but in addition stay present on the altering cyber panorama. Consciousness campaigns involving C-level administration and employees can be utilized to teach and encourage leaders to vary coverage and directives relating to safety.

In Africa, Ghana has made a concerted effort to make cybersecurity a acknowledged family time period. Since 2017, Ghana has performed an annual consciousness marketing campaign throughout October in assist of Cybersecurity Month, offering workshops for each the private and non-private sectors. Cybersecurity Month peaks with the Cybersecurity Week occasion, the place Ghana unveils new cybersecurity providers that the federal government will present to all its constituents. The 2020 theme, “Cybersecurity within the Period of COVID-19,” supplied occasions in all areas of Ghana, in addition to a number of workshops and actions starting from youngster on-line safety, panel discussions, and cybercrime and electronic-evidence workshops.
Whereas such occasions are essential for total consciousness and readiness, organizations wishing to develop cybersecurity applications should first determine present belongings and infrastructure and develop a transparent understanding of the course wherein the enterprise and its supporting applied sciences are headed. Analysis has proven that understanding these key parts will assist organizations decide the abilities vital for brand new crew members and the ability units that should be enhanced in present crew members.
The Future Course in Cybersecurity Human Capital Constructing in Africa
Challenges in creating human capability and in the end human capital aren’t distinctive to Africa. These are human challenges that apply to the worldwide inhabitants. It’s clear that understanding the event of human capital to fulfill present and future wants within the cybersecurity house is critical for continuous on-line security of people and organizations, and for nationwide safety. Organizations should flip their consideration to the cyber expertise and literacy of their workforce with a concentrate on particular roles inside groups and crew features inside organizations.
Our future analysis will concentrate on the intersection of each regional and organizational tradition and its influence on cybersecurity human-capital constructing. Whereas human capital represents the data, ability units, and intangible belongings that add financial worth to people, it’s one thing that can not be statically measured as demonstrated by Enrico Calandro and Patryk Pawlak in Capability Constructing as a Means to Counter Cyber Poverty. What may be measured is the worth that people convey within the type of return on funding (ROI).