Within the final twenty years, community site visitors has elevated greater than 100-fold. Consequently, detecting as we speak’s most regarding cyber assaults, comparable to phishing, drive-by downloads, and ransomware, from that giant stream of site visitors has change into a lot more durable. In essence, community situational consciousness and safety have change into big-data issues, particularly on massive networks.
For years, safety evaluation on massive networks has relied on using community site visitors movement information, comparable to Cisco’s NetFlow. Netflow was designed to pattern and retain crucial attributes of community conversations between TCP/IP endpoints on massive networks with out having to gather, retailer, and analyze all community information. The SEI launched its software for analyzing community movement information, SiLK (System for Web-Degree Data), 18 years in the past. Nonetheless, the rising quantity of community site visitors, and therefore the quantity of associated movement information, has outgrown SiLK’s capability. To shut this hole, the SEI launched Mothra earlier this 12 months.
This SEI Weblog submit will introduce you to Mothra and summarize our latest analysis on enhancements to Mothra designed to deal with large-scale environments. This submit additionally describes analysis aimed toward demonstrating Mothra’s effectiveness at “cloud scale” within the Amazon Internet Providers (AWS) GovCloud surroundings.
Managing the Flood of Community Circulation Information
As total community site visitors has grown, community movement information, comparable to Cisco NetFlow, have additionally grown. Detecting essentially the most severe community assaults requires deep packet inspection (DPI) on these community flows. The DPI course of inspects the info traversing a pc community and might alert, block, re-route, or log this information as required. Nonetheless, whereas DPI extracts extra data on a movement’s security-critical parts, it additionally generates a document a minimum of 5 instances greater than a non-DPI movement document.
The SEI software But One other Flowmeter (YAF) can carry out DPI, amongst different capabilities. YAF is the info assortment element of the SEI’s CERT NetSA Safety Suite. It transforms packets into community flows and exports the flows to Web Protocol Circulation Info Export (IPFIX) gathering processes or an IPFIX-based file format for processing by downstream instruments, specifically the SEI’s SiLK software. SiLK, nonetheless, was not designed to investigate DPI information nor course of the quantity of movement information generated by organizations on the scale of Web service suppliers.
We sensed we had a big-data drawback on our arms, and in 2017 a authorities sponsor requested the SEI to make YAF work with a big-data evaluation software. In response, we created the Mothra evaluation platform to allow scalable analytical workflows that reach past the constraints of standard movement information and the flexibility of our current instruments to course of them. Mothra is a set of open-source libraries for working with community movement information (comparable to Cisco’s Netflow) within the Apache Spark large-scale information analytics engine.
Mothra bridges the beforehand stand-alone instruments of the CERT Community Situational Consciousness (NetSA) Safety Suite and Spark. Different safety options, comparable to antivirus functions or intrusion detection and prevention techniques, may export information to Spark. Mothra allows analysts to entry community movement information alongside these different sources, all inside a standard big-data evaluation surroundings. With all these information sources obtainable for evaluation, organizations with very massive networks can obtain extra complete community situational consciousness.
Just like the SEI’s pre-existing evaluation software, SiLK Mothra was designed to investigate community movement information, particularly these produced by the SEI’s YAF (But One other Flowmeter) software. Mothra transforms YAF output right into a format readable by Apache Spark, and the Mothra platform and in addition
- facilitates bulk storage and evaluation of cybersecurity information with excessive ranges of flexibility, efficiency, and interoperability
- reduces the engineering effort concerned in creating, transitioning, and operationalizing new analytics
- serves all main constituencies throughout the community safety neighborhood, together with information scientists, first-tier incident responders, system directors, and hobbyists
Mothra immediately processes the binary IPFIX format, a regular of the Web Engineering Job Power (IETF). Analysts can effectively pull out simply the items they need, and so they can then use the Spark evaluation engine on the IPFIX information. Mothra permits you to merely drop the info proper in with out having suppose forward about tips on how to rework it. These transformations change the collected information as little as attainable, preserving it for future evaluation.
Analysts can use Mothra to deliver the programming energy of Spark to bear on community movement information from the NetSA Safety Suite. SiLK’s filters permit restricted queries on pure movement datasets. Mothra and Spark allow a lot deeper, versatile queries over DPI-enriched movement to search out way more information of curiosity. For instance, analysts can now pull any type of information they’ll specific as a program and might carry out iterative pulls wherein the info pulled modifications throughout the iterations. They’ll additionally pull information that consists of packets greater than the typical variety of packets throughout the matching set of standards. One thing that might take you a whole lot of scripting in SiLK can now be condensed right down to a half web page of code.
Evaluation of all that movement information requires loads of storage and programming experience. Mothra allows organizations with the infrastructure and personnel to assist Apache Spark, use their experience, and apply DPI analytics to community movement information. This perception will help them consider their present defenses and uncover safety gaps, particularly on infrastructure-level enterprise networks.
Prototyping Mothra at Cloud Scale
Having developed Mothra and proven it to be helpful in on-premises community environments, we subsequent set our sights on answering the next questions:
- Can Mothra be deployed in a cloud surroundings?
- Can a cloud-based deployment work as successfully as Mothra does in an on-premises surroundings?
- How can cloud deployment be finest completed to optimize Mothra’s efficiency?
To reply these questions, we researched strategies for deploying Mothra and its associated system parts within the AWS GovCloud surroundings. Our mission concerned a number of groups that collaborated to deal with code growth, system engineering, and testing. We constructed prototypes of accelerating functionality that progressed towards goal system efficiency. These prototypes ingested billions of movement information per day with applicable content material distributed by the info and made that information obtainable for evaluation in an appropriate period of time.
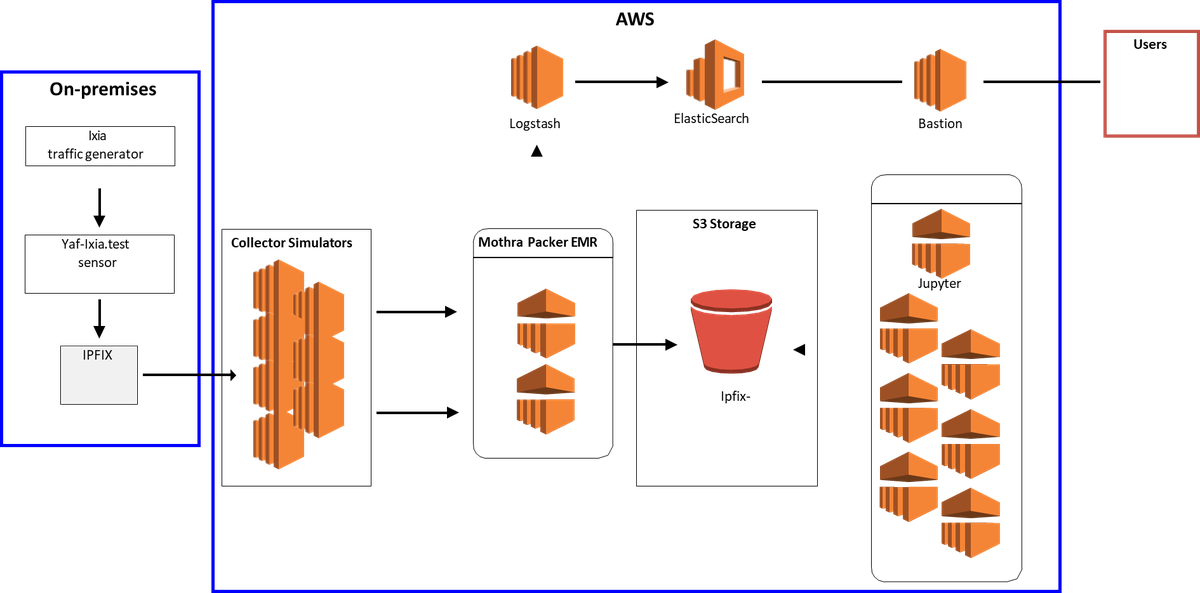
Determine 1 depicts one of many prototypes we developed, which deployed Mothra to Amazon Elastic Map Scale back (EMR) working Spark and backed by the EMR File System (EMRFS) with storage in Amazon S3. EMRFS is an implementation of the Hadoop Distributed File System (HDFS) that every one Amazon EMR clusters use for studying and writing common information from EMR on to S3. EMRFS offers the comfort of storing persistent information in S3 to be used with Hadoop whereas additionally offering options like constant viewing, information encryption, and elasticity.
In conducting our analysis, we shortly decided that Mothra might be simply put in and operated at speeds that clearly met consumer wants when deployed within the cloud. Question efficiency within the cloud surroundings, nonetheless, was suboptimal. To sort out that drawback, we undertook the next work:
- applied a number of system designs within the SEI’s hybrid prototyping surroundings (specifically, we used our Ixia site visitors generator to create an artificial information stream that resulted in a large information repository inside AWS)
- modified configurations as take a look at outcomes are examined to deal with noticed issues
- developed simulators to supply movement volumes that match these noticed on manufacturing techniques
- executed take a look at plans to guage the info ingest course of and consultant question operations
- developed new code to optimize information learn operations
- tuned system providers (e.g., Spark)
Our work confirmed that Mothra might efficiently combine with AWS GovCloud and led us to supply a set of levers that can be utilized for tuning system providers to particular information traits. These levers embody file-read parameters and desired file measurement, that are saved in a system repository. To find out the optimum settings for working within the AWS GovCloud surroundings systematically, we generated a number of Mothra repositories with completely different file eventualities and executed a sequence of checks utilizing a variety of parameter settings.