Cisco helps the Open Cybersecurity Schema Framework and is a launch associate of AWS Safety Lake
The Cisco Safe Technical Alliance helps the open ecosystem and AWS is a valued expertise alliance associate, with integrations throughout the Cisco Safe portfolio, together with SecureX, Safe Firewall, Safe Cloud Analytics, Duo, Umbrella, Net Safety Equipment, Safe Workload, Safe Endpoint, Id Companies Engine, and extra.
Cisco Safe and AWS Safety Lake
We’re proud to be a launch associate of AWS Safety Lake, which permits clients to construct a safety knowledge lake from built-in cloud and on-premises knowledge sources in addition to from their personal purposes. With assist for the Open Cybersecurity Schema Framework (OCSF) normal, Safety Lake reduces the complexity and prices for purchasers to make their safety options knowledge accessible to deal with quite a lot of safety use instances equivalent to menace detection, investigation, and incident response. Safety Lake helps organizations combination, handle, and derive worth from log and occasion knowledge within the cloud and on-premises to offer safety groups higher visibility throughout their organizations.
With Safety Lake, clients can use the safety and analytics options of their alternative to easily question that knowledge in place or ingest the OCSF-compliant knowledge to deal with additional use instances. Safety Lake helps clients optimize safety log knowledge retention by optimizing the partitioning of knowledge to enhance efficiency and cut back prices. Now, analysts and engineers can simply construct and use a centralized safety knowledge lake to enhance the safety of workloads, purposes, and knowledge.
Cisco Safe Firewall serves as a company’s centralized supply of safety info. It makes use of superior menace detection to flag and act on malicious ingress, egress, and east-west site visitors whereas its logging capabilities retailer info on occasions, threats, and anomalies. By integrating Safe Firewall with AWS Safety Lake, via Safe Firewall Administration Heart, organizations will be capable of retailer firewall logs in a structured and scalable method.
eNcore Consumer OCSF Implementation
The eNcore consumer supplies a solution to faucet into message-oriented protocol to stream occasions and host profile info from the Cisco Safe Firewall Administration Heart. The eNcore consumer can request occasion and host profile knowledge from a Administration Heart, and intrusion occasion knowledge solely from a managed gadget. The eNcore software initiates the info stream by submitting request messages, which specify the info to be despatched, after which controls the message movement from the Administration Heart or managed gadget after streaming begins.

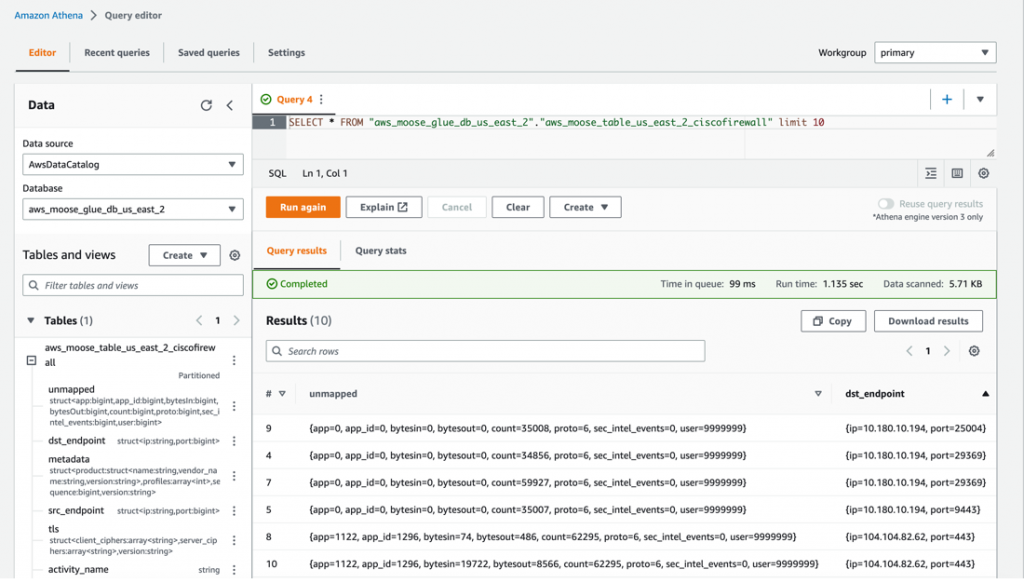
These messages are mapped to OCSF Community Exercise occasions utilizing a collection of transformations embedded within the eNcore code base, appearing as each creator and mapper personas within the OCSF schema workflow. As soon as validated with an inner OCSF schema the messages are then written to 2 sources, first an area JSON formatted file in a configurable listing path, and second compressed parquet information partitioned by occasion hour within the S3 Amazon Safety Lake supply bucket. The S3 directories comprise the formatted log are crawled hourly and the outcomes are saved in an AWS Safety Lake database. From there you will get a visible of the schema definitions extracted by the AWS Glue Crawler, determine fieldnames, knowledge sorts, and different metadata related along with your community exercise occasions. Occasion logs may also be queried utilizing Amazon Athena to visualise log knowledge.
Get Began
To make the most of the eNcore consumer with AWS Safety Lake, first go to the Cisco public GitHub repository for Firepower eNcore, OCSF department.

Obtain and run the cloud formation script eNcoreCloudFormation.yaml.
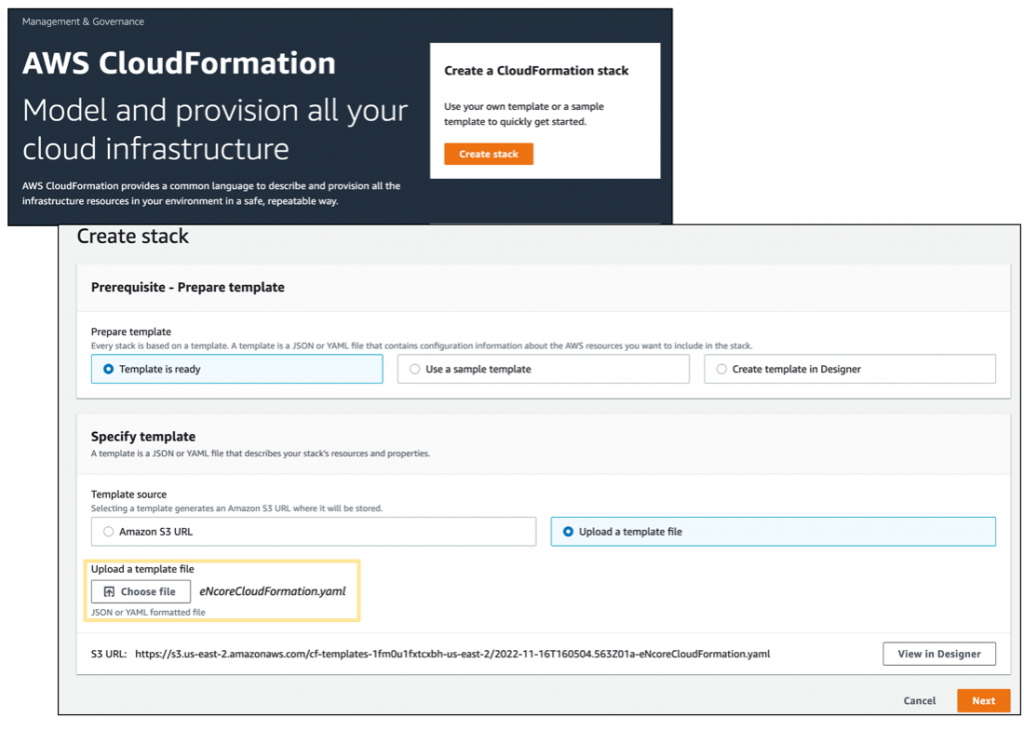
The Cloud Formation script will immediate for extra fields wanted within the creation course of, they’re as follows:
Cidr Block: IP Deal with vary for the provisioned consumer, defaults to the vary proven under
Occasion Kind: The ec2 occasion dimension, defaults to t2.medium
KeyName A pem key file that may allow entry to the occasion
AmazonSecurityLakeBucketForCiscoURI: The S3 location of your Information Lake S3 container.
FMC IP: IP or Area Title of the Cisco Safe Firewall Mangement Portal

After the Cloud Formation setup is full it may possibly take anyplace from 3-5 minutes to provision sources in your atmosphere, the cloud formation console supplies an in depth view of all of the sources generated from the cloud formation script as proven under.
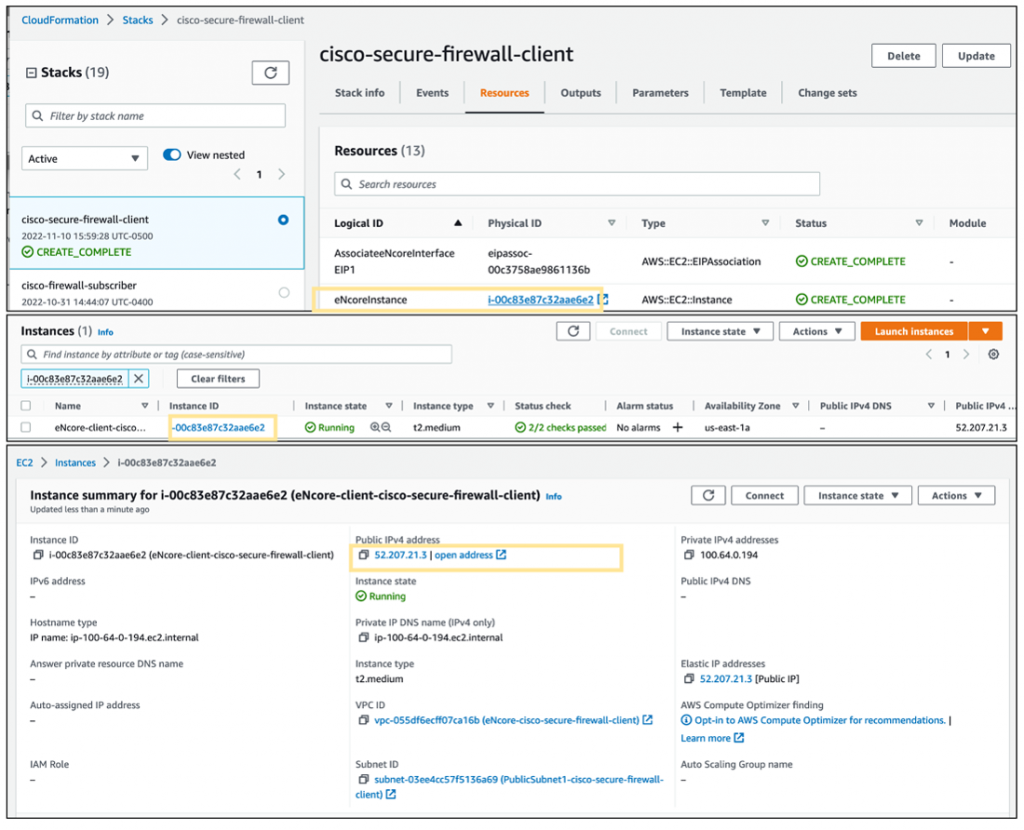
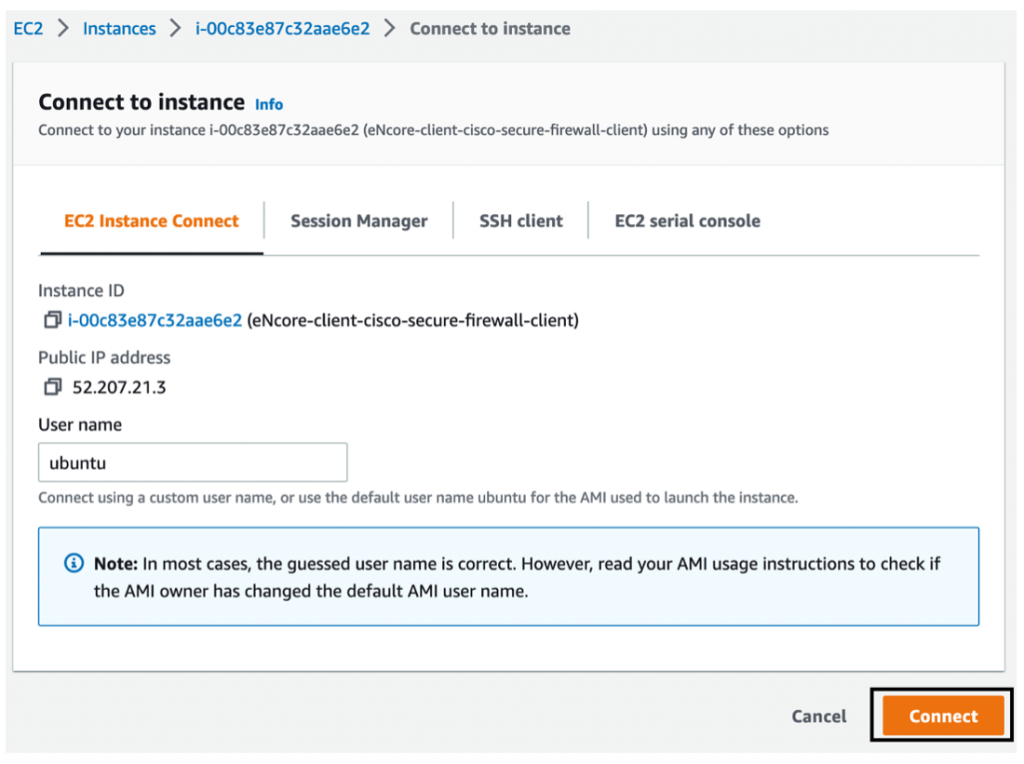
As soon as the ec2 occasion for the eNcore consumer is prepared, we have to whitelist the consumer IP handle in our Safe Firewall Server and generate a certificates file for safe endpoint communication.
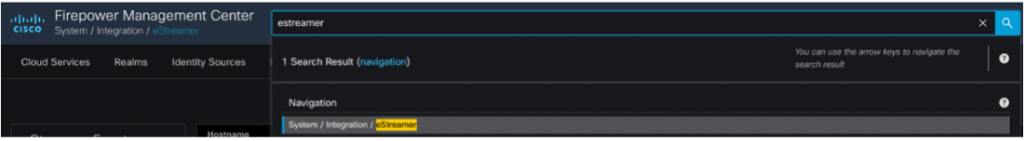
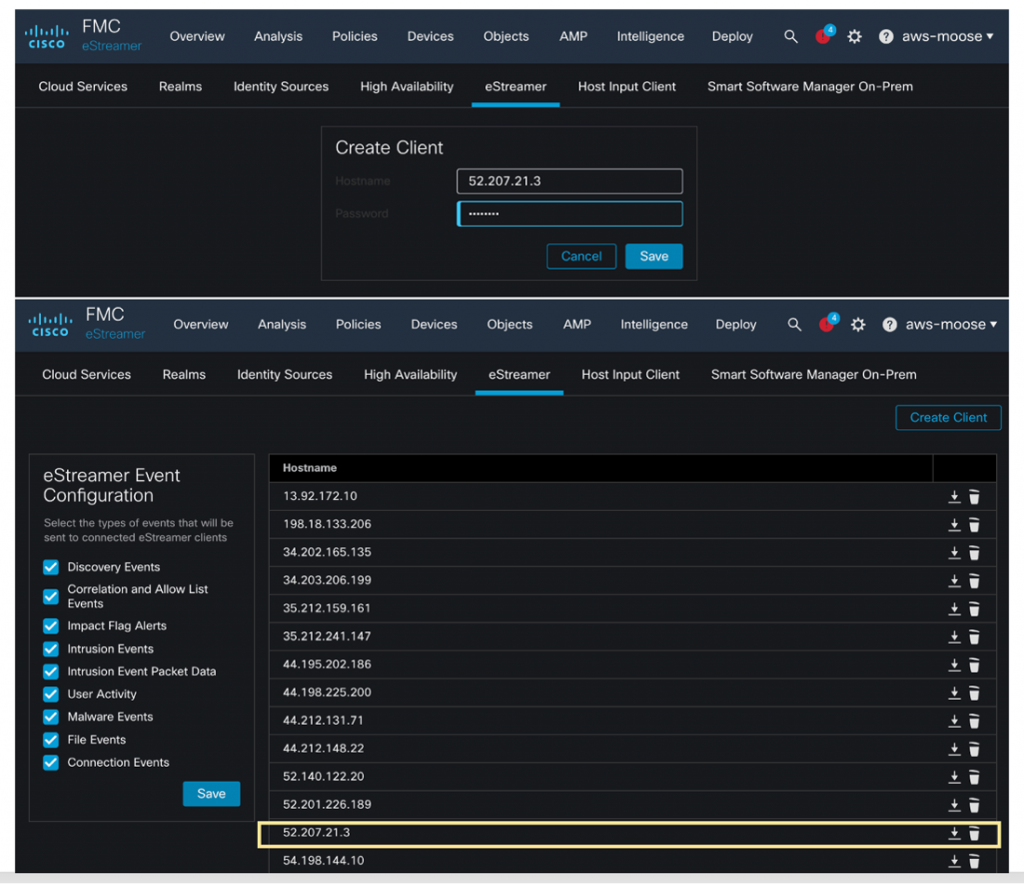
Within the Safe Firewall Dashboard, navigate to Search->eStreamer, to search out the enable listing of Consumer IP Addresses which can be permitted to obtain knowledge, click on Add and provide the Consumer IP Deal with that was provisioned for our ec2 occasion. Additionally, you will be requested to provide a password, click on Save to create a safe certificates file on your new ec2 occasion.
Obtain the Safe Certificates you simply created, and duplicate it to the /encore listing in your ec2 occasion.
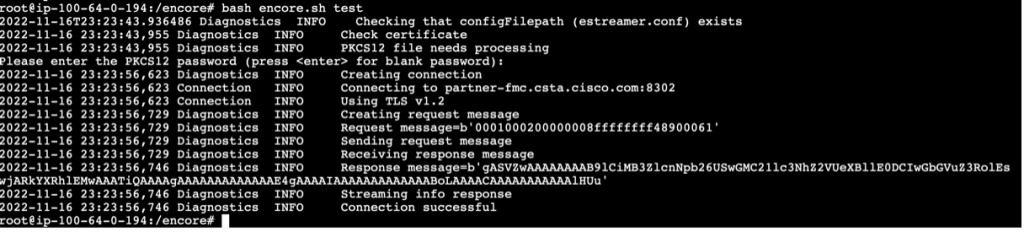
Use CloudShell or SSH out of your ec2 occasion, navigate to the /encore listing and run the command bash encore.sh take a look at
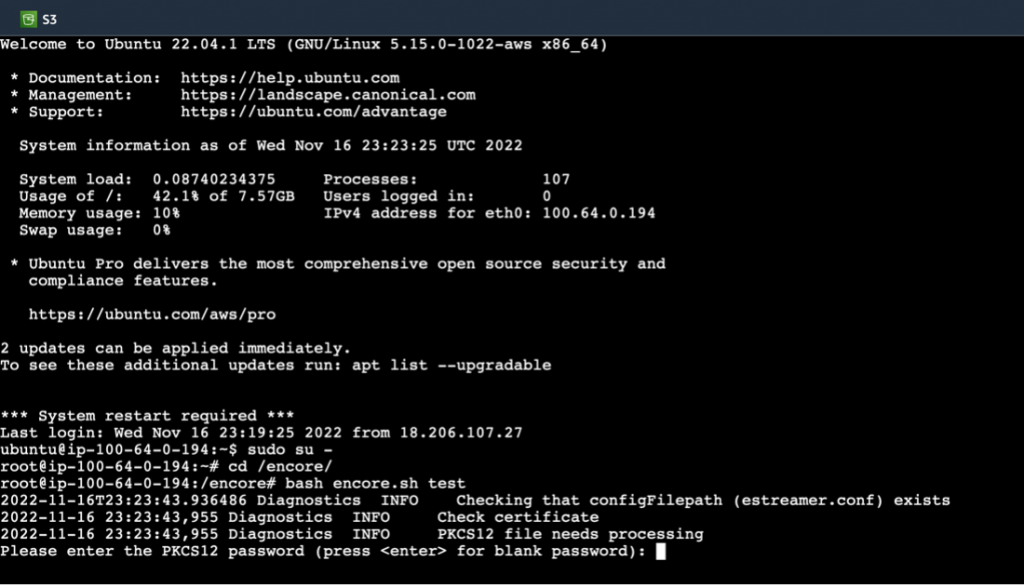
You’ll be prompted for the certificates password, as soon as that’s entered it is best to see a Profitable Communication message as proven under.
Run the command bash encore.sh foreground
This can start the info relay and ingestion course of. We will then navigate to the S3 Amazon Safety Lake bucket we configured earlier, to see OCSF compliant logs formatted in gzip parquet information in a time-based listing construction. Moreover, an area illustration of logs is out there underneath /encore/knowledge/* that can be utilized to validate log file creation.

Amazon Safety Lake then runs a crawler activity each hour to parse and eat the logs information within the goal s3 listing, after which we are able to view the ends in Athena Question.
Extra info on the way to configure and tune the encore eStreamer consumer might be discovered on our official web site, this contains particulars on how filter sure occasion sorts to focus your knowledge retention coverage, and pointers for efficiency and different detailed configuration settings.
Take part within the public preview
You’ll be able to take part within the AWS Safety Lake public preview. For extra info, please go to the Product Web page and evaluate the Person Information.
re:Invent
When you are at AWS re:Invent, go see a demo video of the Safety Lake integrations within the Cisco Sales space #2411, from November 29 to December 2, 2022, on the Cloud, Community and Person Safety with Duo demo station.
Study extra about Cisco and AWS on the Cisco Safe Technical Alliance web site for AWS.
Acknowledgement
Thanks to Seyed Khadem-Djahaghi, who spend lengthy hours working with the beta to develop this integration and is the first for developer of eNore.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safe Social Channels
Share:






