AI know-how has turn out to be an extremely necessary a part of most IT capabilities. One of many many causes IT professionals are investing in AI is to fortify their digital safety.
The most effective ways in which cybersecurity professionals are leveraging AI is by using SAST methods.
AI Solidifies Community Safety with Higher SAST Protocols
AI know-how has led to plenty of new cybersecurity threats. Luckily, organizations can even use AI know-how to struggle cybercrime as effectively.
Each single day, all kinds of latest functions and features of code are being launched. A giant a part of what allows this fixed deployment of latest functions is a testing course of referred to as static utility safety testing, or SAST. It analyzes the supply code created by builders or organizations to find safety flaws. An utility is analyzed by SAST previous to having its code constructed. It’s continuously known as “white field testing.”
As of late, organizations want to undertake the shift left methodology, which requires issues to be corrected as quickly as they’re found. Due to this, SAST takes place extraordinarily early on within the software program improvement lifecycle (SDLC).
AI has made it simpler than ever for IT networks to enhance SAST. Neil Okay. Jones mentioned the position of synthetic intelligence in SAST improvement in his put up titled The Magic of AI in Static Software Safety Testing in Dzone.
This works as a result of SAST doesn’t require a well-functioning software program; reasonably, it merely wants machine studying codes which are at present being developed, which it then analyzes to seek out vulnerabilities. These AI codes additionally assist builders detect SAST vulnerabilities within the early levels of improvement, so they could shortly resolve the problems with out releasing susceptible code into manufacturing, which might pose a menace to the infrastructure of the corporate.
For contemporary-day functions that use containers and Kubernetes, SAST is used for Kubernetes safety to guard deployments by figuring out potential vulnerabilities within the codebase earlier than the code is put into manufacturing. This permits organizations to repair points early on and prevents any potential vulnerabilities from affecting the ultimate product. This is among the finest methods for corporations to make use of AI to enhance community safety.
How Does a Trendy SAST Technique Work and What Function Does AI Play in It?
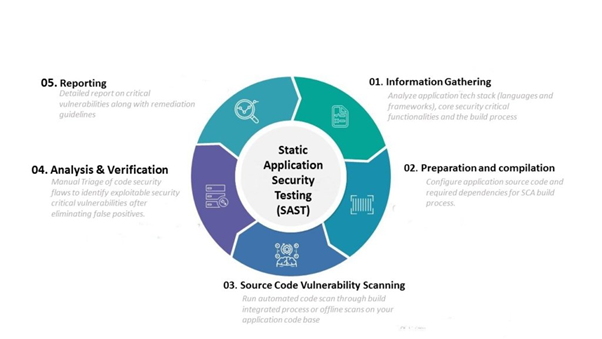
The current SAST method is kind of effectively developed, particularly because it has improved because of new advances in AI. This know-how additionally helps it make use of all kinds of instruments, all of which contribute to the method of fixing smaller bugs and vulnerabilities that will exist within the code.
There are a selection of potential vulnerabilities that must be addressed, akin to open supply provide chain assaults, that might occur due to issues like outdated packages. New developments in AI have made it simpler to detect these issues, which helps enhance the safety of the general utility.
What are among the ways in which AI has helped enhance SAST? A number of the advantages have been developed by AI scientists at IBM.
These consultants used IBM’s AI utility referred to as “Watson” to higher determine safety vulnerabilities. They got here up with an Clever Discovering Analytics (IFA) device, which had a 98% accuracy with detecting safety vulnerabilities.
You may be taught extra about the advantages of utilizing AI for SAST within the following YouTube video by IBM.
Let’s have a dialog in regards to the approaches which are at present being taken to deal with issues of this nature.
Securing the Dependencies
Purposes depend on numerous completely different dependencies to be able to operate correctly. Not solely do they make the duty simpler for the software program builders, however in addition they help builders in writing code that’s dependable and efficient. Attributable to the truth that nearly all of these dependencies are open supply and subsequently might embody vulnerabilities, it’s essential to carry out common updates on them.
There may very well be numerous dependents inside an utility. Thus, it’s not possible for these dependencies to be monitored manually. Doing so would contain a big quantity of effort and will additionally result in errors attributable to handbook intervention. In mild of this, companies sometimes make use of dependency administration instruments.
Such instruments, after checking for accessible updates within the dependencies inside a predetermined period of time, open a pull request for every replace that’s accessible. They’re additionally capable of mix requests if that has been permitted by the consumer. Due to this fact, they discover methods to remove the dangers related to the dependencies.
Performing Code Critiques
Code is the only real determinant of an utility’s habits, and errors within the code are the foundation reason for safety flaws. If these vulnerabilities have been to be despatched to manufacturing, they could create all kinds of issues, akin to SQL injection, and will even compromise the infrastructure of the whole group. Due to this, it’s completely mandatory to make use of the shift-left method earlier than placing code into manufacturing.
A big variety of SAST instruments are being utilized by organizations for the aim of deploying code evaluations. These code overview instruments carry out an in-depth evaluation of the code earlier than it’s added to any repository. If the code has any of the recognized vulnerabilities, they won’t permit it to be deployed till the issues have been mounted. Due to this fact, it’s helpful for the shift-left technique, which is predicated on the idea of remedying a vulnerability as quickly as it’s found, and solely pushing safe code into manufacturing.
There’s a massive number of softwares accessible in the marketplace, and a few of them allow corporations and different organizations to patch their code as quickly as safety flaws are discovered. The patch will be deployed with just some mouse clicks, and there are sometimes a number of distinct choices accessible to select from when fixing a selected vulnerability.
Secret Scannings
As of late, utility are depending on a big quantity of integration, akin to cost gateways, error detection, and so forth. Normally, these APIs will execute, and authentication shall be carried out utilizing the API key and the key.
These keys should be required to have an satisfactory stage of safety, such because the Stay API key for Stripe cost needing to have an satisfactory stage of safety. If this data is leaked, anyone can entry the delicate cost knowledge and withdraw or view it. In consequence, a number of companies have begun utilizing secret scanning instruments.
These instruments mainly undergo the code to see whether or not it comprises any of the recognized API keys; if it does, the device prevents the code from being revealed into manufacturing. It’s potential for the code overview device itself to offer these options. Alternatively, a corporation might simply write their very own proprietary device to be able to determine issues of this sort.
AI Makes SAST Extra Efficient than Ever
Firms are utilizing AI know-how to cope with a number of latest cybersecurity threats. The most effective functions of AI is through the use of new SAST protocols to determine safety threats.
Since corporations at the moment are transitioning to a shift-left technique, they’re using SAST instruments, which, in a nutshell, uncover vulnerabilities as quickly as they’re coded and repair them. That is inflicting the shift left method to turn out to be more and more fashionable. If the code has any flaws that may very well be exploited by malicious actors, the deployment shall be blocked till the issues are mounted.
Firms now have entry to all kinds of various strategies, akin to dependency administration instruments, secret scanning instruments, and so forth, which not solely produce the right safe code deployment but in addition produce the right patches for vulnerabilities as quickly as they’re found within the coding part.