The transfer to a cloud atmosphere supplies important advantages. For instance, cloud assets could be scaled shortly, up to date regularly, and broadly accessed with out geographic limitations. Realizing these advantages, nonetheless, requires organizations to handle related organizational and technical dangers successfully. This weblog submit presents a prototype set of cloud adoption threat components and describes a technique that managers can make use of to evaluate their cloud initiatives in opposition to these threat components. This submit is tailored and excerpted from a lately printed white paper. It additionally builds on foundational work that’s introduced in an SEI weblog submit on cloud migration dangers, threats, and vulnerabilities and an SEI technical report on cloud safety finest practices.
Downside Area
Cloud adoption impacts many enterprise models throughout a corporation and might change how these enterprise models function. Senior leaders should steadiness a wide range of stakeholder pursuits, alternatives, dangers, and points. Know-how builders would possibly need rapid entry to new applied sciences or companies. On the identical time, finance managers would possibly favor initiatives that scale back prices and supply a excessive return on funding. If left unchecked, these competing objectives can forestall a corporation from optimizing its funding in cloud computing.
In some organizations, managers of enterprise models have the authority to constitution cloud initiatives based mostly on the wants of their models. In such instances, a cloud initiative would possibly align with a enterprise unit’s parochial objectives. If these native advantages don’t align with the group’s enterprise technique and objectives the general group won’t obtain the advantages that senior administration needs. This misalignment of group and business-unit objectives, and the dearth of a coordinated governance, can put cloud adoption in danger.
Quite a lot of organizational and technical components can adversely have an effect on a corporation’s cloud initiative. Organizational components embody an inadequate organizational cloud technique, ill-defined organizational roles and tasks, inadequate technical talent set, and poor change administration practices. Technical components embody insufficient structure and design; poor integration of on-premises and cloud applied sciences; and cloud service that lacks wanted agility, availability, and safety properties. Managers want an efficient technique to assess dangers that may have an effect on a profitable adoption of cloud companies.
Mission Threat Diagnostic (MRD) Methodology
Because the early Nineteen Nineties, the SEI has carried out analysis and growth in threat administration and has utilized threat administration strategies, instruments, and methods throughout the software program lifecycle (together with acquisition, growth, and operations) and provide chain. As well as, previous SEI analysis examined numerous varieties of threat, together with software program growth threat, system acquisition threat, operational threat, mission threat, cybersecurity engineering threat, incident administration threat, and info safety threat. A key results of our analysis into the follow of threat administration was the event of the Mission Threat Diagnostic (MRD) methodology, which is a mission-oriented method for assessing threat in mission threads, enterprise processes, and organizational initiatives.
The overarching objective of the MRD methodology is to find out the extent to which a mission thread, enterprise course of, or organizational initiative is positioned to realize its mission goal(s). Up to now, we now have piloted the MRD in software program acquisition and growth, cybersecurity incident administration, software program safety, software program supply-chain, and enterprise portfolio administration, amongst others. This weblog submit describes how we’re proposing to use the MRD to the adoption of cloud companies.
An MRD evaluation usually requires an evaluation workforce to guage 15-25 threat components for a given set of aims. A query for every threat issue is documented in a format prescribed in the MRD methodology description. Every threat query is a sure/no query that’s phrased from the success perspective. For instance, one of many MRD questions for cloud adoption is: Does the group’s enterprise case justify the choice to maneuver to the cloud?
Respondents can choose one of many following decisions for an MRD query:
- Sure— The reply is sort of actually “sure.” Nearly no uncertainty exists. There’s little or no likelihood that the reply may very well be “no.” (~ > 95% likelihood of sure)
- Probably sure—The reply is more than likely “sure.” There’s some likelihood that the reply may very well be “no.” (~ 75% likelihood of sure)
- Equally probably—The reply is simply as prone to be “sure” or “no.” (~ 50% likelihood of sure)
- Probably no—The reply is more than likely “no.” There’s some likelihood that the reply may very well be “sure.” (~ 25% likelihood of sure)
- No—The reply is more than likely “no.” There’s some likelihood that the reply may very well be “sure.” (~ < 5% likelihood of sure)
The rationale for the response to every driver query also needs to be documented because it captures the the explanation why the response was chosen. Any proof supporting the rationale, such because the outcomes of interviews with system stakeholders and knowledge cited from system documentation, also needs to be cited. Recording the rationale and proof is necessary for validating the info and related info merchandise, for historic functions, and for growing classes discovered.
Cloud Adoption Threat Elements
We have now developed a prototype set of 24 threat components for cloud adoption. They have been developed utilizing printed cloud-adoption studies and frameworks, in addition to enter from folks with experience in cloud adoption. Take into account these threat components to be a starter set that may be tailor-made to distinctive environments. Threat components that share widespread organizational and administration attributes are assigned to a standard space. We established the next areas for the MRD cloud adoption threat components:
- planning and preparation
- governance and administration
- organizational functionality
- atmosphere
- engineering lifecycle
- high quality of service
Assigning threat components to areas facilitates leveraging widespread threat mitigation actions based mostly on shared threat traits. The rest of this weblog submit describes the danger components and related MRD questions for every space.
Planning and Preparation
The profitable adoption of cloud applied sciences begins with a corporation’s planning and preparation actions. Efficient planning and preparation present a strong basis for a cloud initiative by guaranteeing that the group has ample funding and assets in place to help the cloud initiative. The Planning and Preparation space contains the next threat components and related MRD questions:

Governance and Administration
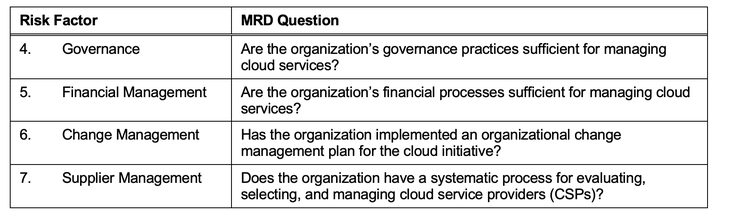
Governance focuses on the alignment of the group’s IT technique and objectives with its enterprise technique and objectives. An efficient governance program is designed to maximise the enterprise worth of IT investments whereas minimizing the related dangers. Administration is the coordination and administration of duties to realize enterprise objectives. A company’s administration actions have to be applied in accordance with the group’s system of governance guidelines, practices, and processes. The Governance and Administration space contains the next threat components and related MRD questions:
Organizational Functionality
Organizational functionality is the distinctive mixture of individuals, processes, and applied sciences that differentiates a corporation and allows it to execute its technique. A company’s capabilities allow it to carry out a coordinated set of duties, using organizational assets, for the aim of reaching a particular set of enterprise aims. For cloud adoption, the capabilities of curiosity allow the event and implementation of a scientific framework for adopting cloud companies. The Organizational Functionality space contains the next threat components and related MRD questions:

Setting
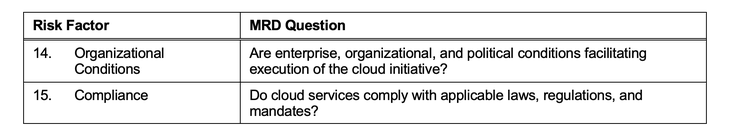
A company’s atmosphere consists of inside and exterior circumstances that affect a corporation’s efficiency, operations, and assets. Inner circumstances embody the group’s construction, tradition, and politics, in addition to its communication infrastructure. Exterior circumstances embody any constraints {that a} program inherits from its mum or dad group(s) or from the broader enterprise atmosphere. Constraints can embody restrictions imposed by legal guidelines and laws, in addition to limitations with companies offered by third events. The Setting space include the next threat components and related MRD questions:
Engineering Lifecycle
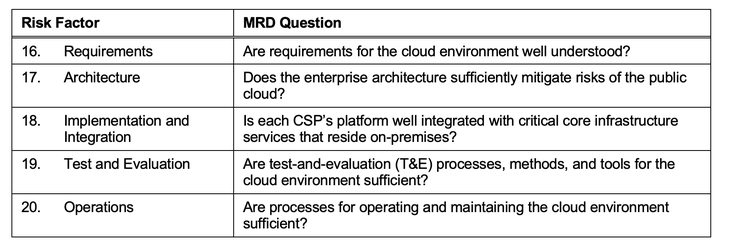
Threat components for a cloud initiative want to deal with each organizational and technical points that may have an effect on the initiative’s potential for achievement. Till this level, we now have targeted on organizational threat components associated to preparation and planning, governance and administration, group functionality, and atmosphere. We now flip our consideration towards the technical points, starting with the engineering lifecycle threat components. The engineering lifecycle addresses the phases of a system’s growth, together with idea growth, necessities, structure, implementation, take a look at and analysis, deployment, operations, and disposal. Technical points associated to the lifecycle embody lacking or incomplete necessities, insufficient structure, poor integration of on-premises and cloud applied sciences, and insufficient operational help for cloud applied sciences. The Engineering Lifecycle space contains the next threat components and related MRD questions:
High quality-of-Service
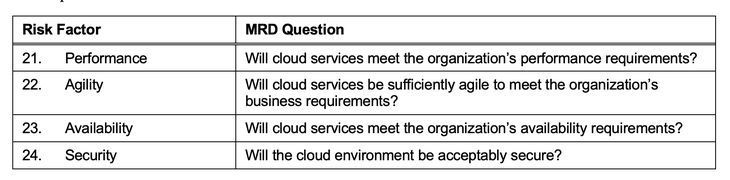
High quality-of-service (QoS) describes or measures how nicely cloud companies are anticipated to satisfy the wants and necessities of customers throughout operations. This space examines dangers which can be inherent within the technical resolution offered by a mission or initiative. The QoS service threat components give attention to the correctness and completeness of the applied technical resolution. For a cloud initiative, QoS addresses the efficiency and performance offered by a cloud atmosphere, in addition to high quality attributes, reminiscent of availability and safety. The High quality-of-Service space contains the next threat components and related MRD questions:
Piloting the MRD for Cloud Adoption
The cloud adoption threat components described above are a protype set that have been developed utilizing printed info on cloud adoption frameworks and enter from SEI technical employees who’ve expertise with each cloud computing and know-how adoption initiatives. Up to now, these threat components haven’t been piloted within the subject. Those that intend to use the danger components on this submit needs to be aware that the components haven’t been vetted within the subject by SEI builders. Nonetheless, the danger components do incorporate info from dependable sources, together with Amazon, Microsoft, and Google.
We view the publication of this weblog and related white paper as an preliminary step within the growth of cloud adoption threat components somewhat than the fruits of our work on this space. A possible subsequent step is to pilot the present model of the MRD for cloud adoption with organizations that plan to undertake cloud companies. Future growth and transition actions will finally be decided by the suggestions that we obtain from folks all through the neighborhood. Irrespective of which transition actions are applied, we consider that the content material introduced on this weblog will assist organizations to handle their dangers extra successfully as they plan and handle the adoption of cloud applied sciences.

