Unified risk administration is regarded as a common resolution for a lot of causes. Initially, it’s suitable with virtually any {hardware}. As a enterprise or an MSP, you do not have to hassle with leasing or subleasing costly tools. There isn’t a must chase your shoppers to return your expensive {hardware}. The all-in-one UTM resolution will save you time and money & make work routine much less irritating.
Nonetheless, solely buying a complicated IT resolution would possibly find yourself in a waste of cash, if the seller doesn’t tailor it up particularly to your wants. Extra troubles happen in case your workers doesn’t have a lot IT background or just is just not tech-savvy sufficient.
We put collectively a compilation of the perfect use instances of SafeUTM so you’ll be able to see combine such an answer into your infrastructure & allow you to in the reduction of on pointless bills of all types.
UTM as a lifesaver for enterprise cybersecurity
Massive steel trade firm of 4,500 customers
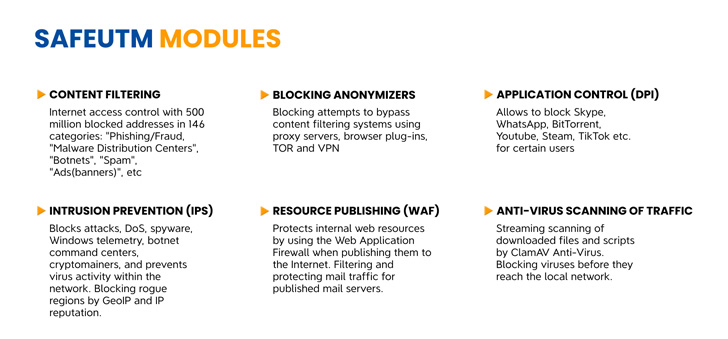
Among the many challenges confronted earlier than implementing the answer was a requirement to have an extra community perimeter safety. The corporate was additionally not receiving sufficient updates & had poor tech assist for the firewall. We put in SafeUTM as a proxy, configured content material filtering based on company requirements & added a built-in internet antivirus for added safety, because the shopper requested.
Worldwide financial institution of two,000 customers
As a result of a sudden swap to distant & hybrid work mode, the group discovered it arduous to maintain their cybersecurity layers robust. In addition they skilled a downtime as a consequence of inoperability of the answer, and it was essential to construct a distributed community.
What SafeUTM did was construct a VPN community for distant connection of staff to their workplaces, establishing two-factor authentication to guard towards connecting untrusted customers & site-to-site connection at department workplaces through IPSec, and configuring a fault tolerance cluster.
Massive division of a railway firm, 2,000 customers
Their present resolution was manner too outdated & desperately wanted substitute. As a result of such an answer didn’t meet the sport guidelines of recent cybersecurity, the corporate had quite a few hacks & different data safety incidents. This triggered some misuse of community sources. Due to this fact, all the community configuration was saved and migrated to the SafeUTM gateway. Using community bandwidth was optimized, intrusion prevention system enabled, leading to common requests for unauthorized entry to the community.As well as, we configured utility entry management with a view to restrict using undesirable software program & company electronic mail safety when utilizing SafeUTM gateway as mail relay.
How do smaller organizations profit with a UTM?
State college of upper training, 500 customers
The college had a number of points {that a} UTM may repair: content material filter base was solely related to English-speaking customers, filtering settings for various person teams weren’t versatile or customizable. There have been assaults on the revealed internet useful resource & the group didn’t personal a mail server. Respectively, we configured content material filtering utilizing a base related to the languages spoken within the space & primarily based on AD safety teams. Internet useful resource was revealed via reverse proxy, preconfigured WAF was enabled, and HTTP requests redirected. As to the mail problem, we configured the mail server at SafeUTM utilizing built-in filtering and anti-spam lists.
Small buying and selling firm of 200 customers
The corporate had used a generic router to guard the perimeter, which was not efficeint in any respect. Along with that, there was no reporting system & no skill to replace resolution settings towards fashionable threats as a consequence of a heavy workload of the system administrator. What SafeUTM did was configuring modules of content material filtering, utility management, intrusion prevention system with automated updating of filtering databases & automated assortment and sending of studies on the handed site visitors. As we do for another shopper, we supplied all essential help in configuring and implementing the answer throughout the pilot part.
A UTM resolution in right this moment’s circumstances is certainly the best alternative for a corporation that’s conscious of all of the methods lack of cybersecurity would possibly lead. Be at liberty to chat with our UTM engineers to learn the way precisely such an answer could be tailor-made up to your particular case.