| Feb 25, 2023 |
|
|
|
(Nanowerk Information) Detailed digital copies of bodily objects, referred to as digital twins, are opening doorways for higher merchandise throughout automotive, well being care, aerospace and different industries. In line with a brand new examine, cybersecurity may match neatly into the digital twin portfolio.
|
|
As extra robots and different manufacturing tools change into remotely accessible, new entry factors for malicious cyberattacks are created. To maintain tempo with the rising cyber menace, a group of researchers on the Nationwide Institute of Requirements and Expertise (NIST) and the College of Michigan devised a cybersecurity framework that brings digital twin expertise along with machine studying and human experience to flag indicators of cyberattacks.
|
|
In a paper revealed in IEEE Transactions on Automation Science and Engineering (“Cyber-Assault Detection Digital Twins for Cyber-Bodily Manufacturing Methods”), the NIST and College of Michigan researchers demonstrated the feasibility of their technique by detecting cyberattacks aimed toward a 3D printer of their lab. In addition they notice that the framework could possibly be utilized to a broad vary of producing applied sciences.
|
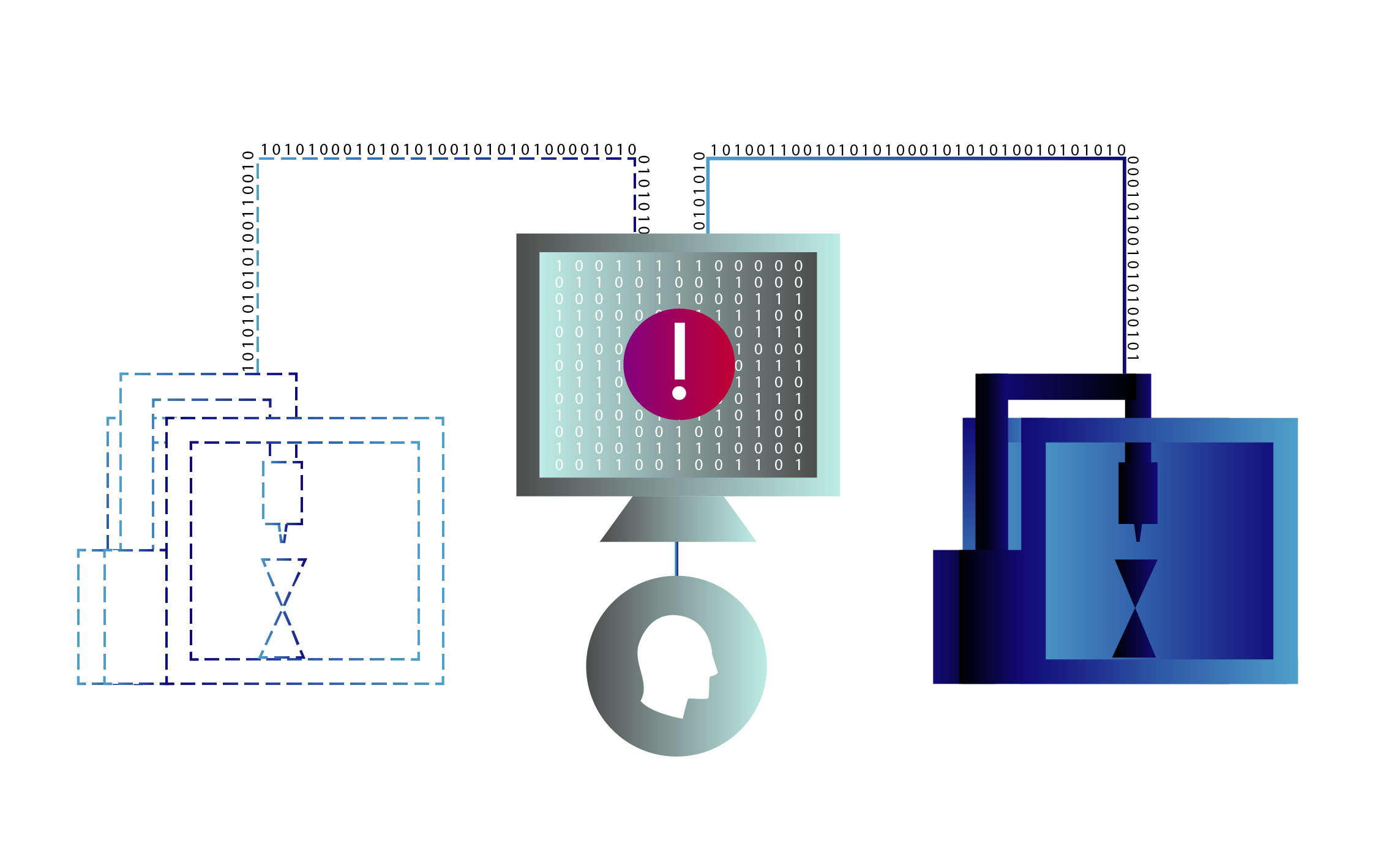 |
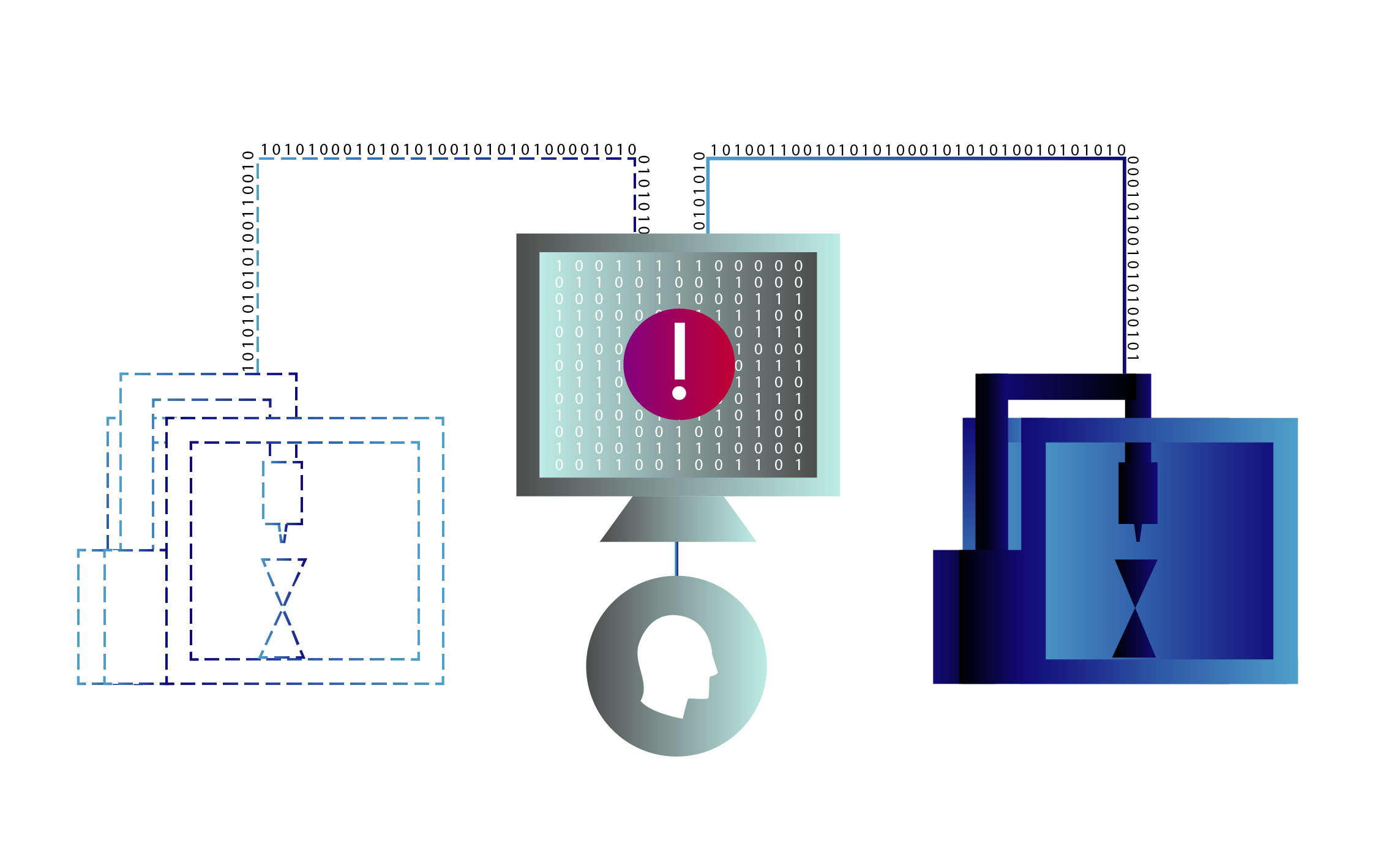
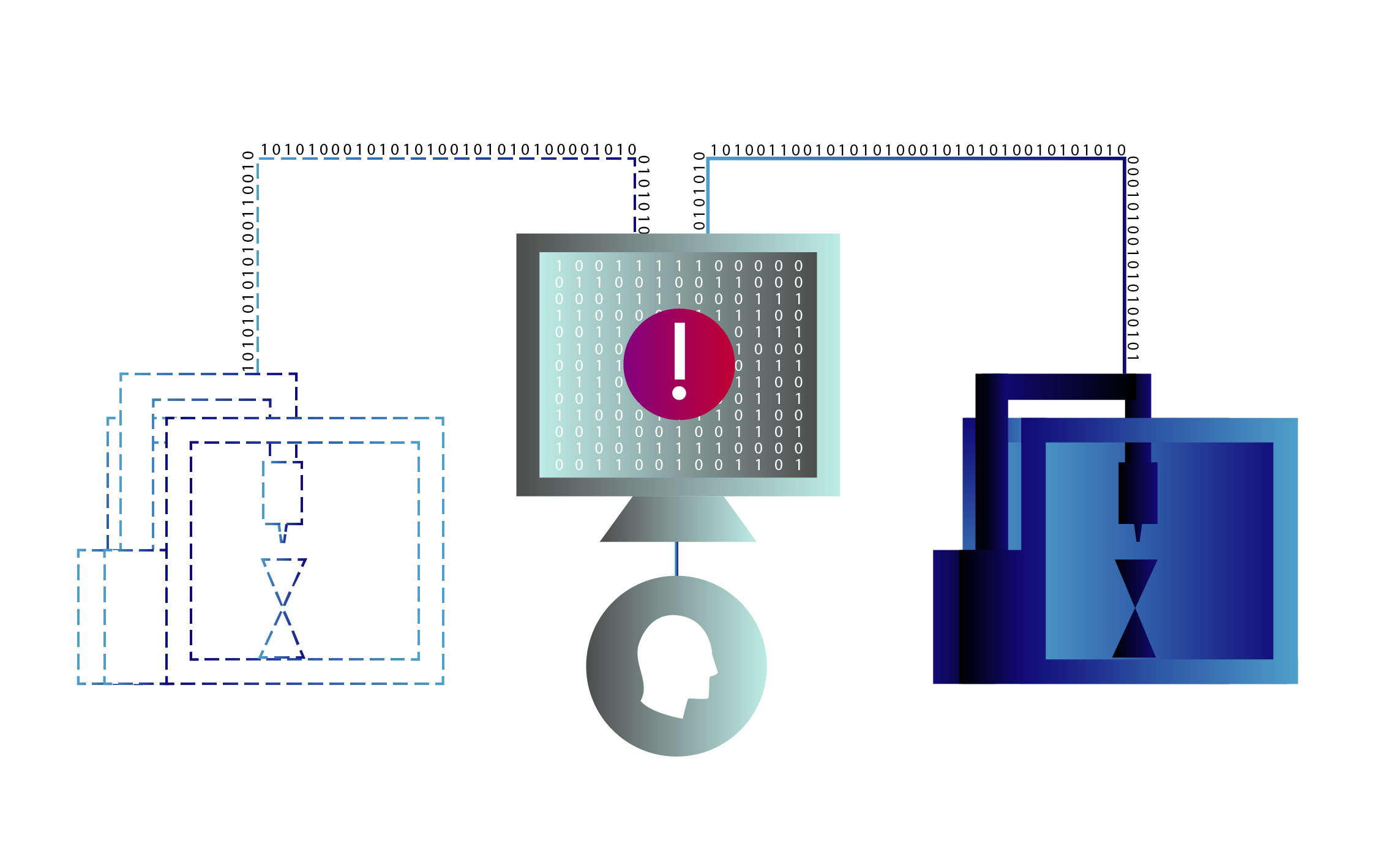
| A graphic illustrates data flowing from each actual and digital 3D printers on both aspect of a pc monitored by an individual. A brand new and improved technique for detecting cyberattacks on manufacturing techniques, comparable to 3D printers, entails utilizing AI to watch a digital twin that mimics and is fed real-time information from the bodily system. (Picture: N. Hanacek, NIST)
|
|
Cyberattacks might be extremely refined and thus tough to detect or differentiate from different, generally extra routine, system anomalies. Operational information describing what is happening inside machines — sensor information, error indicators, digital instructions being issued or executed, for example — might assist cyberattack detection. Nevertheless, straight accessing this type of information in close to actual time from operational expertise (OT) units, comparable to a 3D printer, might put the efficiency and security of the method on the manufacturing unit flooring in danger.
|
|
“Sometimes, I’ve noticed that manufacturing cybersecurity methods depend on copies of community visitors that don’t all the time assist us see what is happening inside a chunk of equipment or course of,” stated NIST mechanical engineer Michael Pease, a co-author of the examine. “Consequently, some OT cybersecurity methods appear analogous to observing the operations from the skin by a window; nonetheless, adversaries may need discovered a manner onto the ground.”
|
|
With out trying underneath the hood of the {hardware}, cybersecurity professionals could also be leaving room for malicious actors to function undetected.
|
Taking a Look within the Digital Mirror
|
|
Digital twins aren’t your run-of-the-mill laptop fashions. They’re intently tied to their bodily counterparts, from which they extract information and run alongside in close to actual time. So, when it’s not attainable to examine a bodily machine whereas it’s in operation, its digital twin is the following smartest thing.
|
|
Lately, digital twins of producing equipment have armed engineers with an abundance of operational information, serving to them accomplish quite a lot of feats (with out impacting efficiency or security), together with predicting when components will begin to break down and require upkeep.
|
|
Along with recognizing routine indicators of damage and tear, digital twins might assist discover one thing extra inside manufacturing information, the authors of the examine say.
|
|
“As a result of manufacturing processes produce such wealthy information units — temperature, voltage, present — and they’re so repetitive, there are alternatives to detect anomalies that stick out, together with cyberattacks,” stated Daybreak Tilbury, a professor of mechanical engineering on the College of Michigan and examine co-author.
|
|
To grab the chance offered by digital twins for tighter cybersecurity, the researchers developed a framework entailing a brand new technique, which they examined out on an off-the-shelf 3D printer.
|
|
The group constructed a digital twin to emulate the 3D printing course of and supplied it with data from the actual printer. Because the printer constructed a component (a plastic hourglass on this case), laptop applications monitored and analyzed steady information streams together with each measured temperatures from the bodily printing head and the simulated temperatures being computed in actual time by the digital twin.
|
|
The researchers launched waves of disturbances on the printer. Some had been harmless anomalies, comparable to an exterior fan inflicting the printer to chill, however others, a few of which brought about the printer to incorrectly report its temperature readings, represented one thing extra nefarious.
|
|
So, even with the wealth of knowledge at hand, how did the group’s laptop applications distinguish a cyberattack from one thing extra routine? The framework’s reply is to make use of a strategy of elimination.
|
|
The applications analyzing each the actual and digital printers had been pattern-recognizing machine studying fashions skilled on regular working information, which is included within the paper, in bulk. In different phrases, the fashions had been adept at recognizing what the printer regarded like underneath regular circumstances, additionally which means they might inform when issues had been out of the abnormal.
|
|
If these fashions detected an irregularity, they handed the baton off to different laptop fashions that checked whether or not the unusual indicators had been in keeping with something in a library of recognized points, such because the printer’s fan cooling its printing head greater than anticipated. Then the system categorized the irregularity as an anticipated anomaly or a possible cyber menace.
|
|
Within the final step, a human knowledgeable is supposed to interpret the system’s discovering after which decide.
|
|
“The framework supplies instruments to systematically formalize the subject material knowledgeable’s information on anomaly detection. If the framework hasn’t seen a sure anomaly earlier than, an issue knowledgeable can analyze the collected information to offer additional insights to be built-in into and enhance the system,” stated lead-author Efe Balta, a former mechanical engineering graduate scholar on the College of Michigan and now a postdoctoral researcher at ETH Zurich.
|
|
Usually talking, the knowledgeable would both affirm the cybersecurity system’s suspicions or train it a brand new anomaly to retailer within the database. After which as time goes on, the fashions within the system would theoretically study increasingly, and the human knowledgeable would wish to show them much less and fewer.
|
|
Within the case of the 3D printer, the group checked its cybersecurity system’s work and located it was capable of appropriately type the cyberattacks from regular anomalies by analyzing bodily and emulated information.
|
|
However regardless of the promising displaying, the researchers plan to check how the framework responds to extra different and aggressive assaults sooner or later, guaranteeing the technique is dependable and scalable. Their subsequent steps will possible additionally embody making use of the technique to a fleet of printers without delay, to see if the expanded protection both hurts or helps their detection capabilities.
|
|
“With additional analysis, this framework might probably be an enormous win-win for each upkeep in addition to monitoring for indications of compromised OT techniques,” Pease stated.
|