Ransomware: up to date threats, the best way to forestall them and the way the FBI may also help
In April 2021, Dutch supermarkets confronted a meals scarcity. The trigger wasn’t a drought or a sudden surge within the demand for avocados. Somewhat, the rationale was a ransomware assault. Previously years, corporations, universities, faculties, medical services and different organizations have been focused by ransomware risk actors, turning ransomware into the web’s most extreme safety disaster.
The Ransomware Panorama
Ransomware has existed for greater than 30 years, however it turned a profitable supply of earnings for cyber actors and gangs previously decade. Since 2015, ransomware gangs have been focusing on organizations as an alternative of people. Consequently, ransom sums have elevated considerably, reaching tens of millions of {dollars}.
Ransomware is efficient as a result of it pressures victims in two, complementary methods. First, by threatening victims to destroy their information. Second, by threatening to publicize the assault. The second risk has an oblique influence, but it’s simply as severe (if no more). Publication may set off regulatory and compliance points, in addition to detrimental long-term model results.
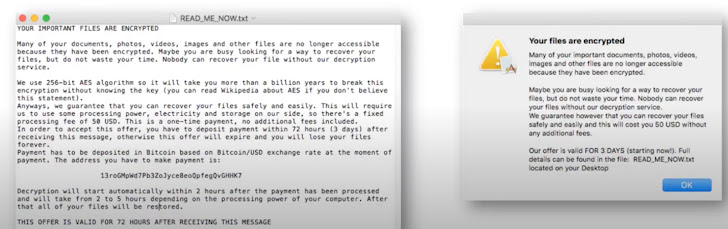
Listed below are some examples of actual ransomware notes:
Ransomware as a Service (RaaS) has grow to be probably the most widespread kind of ransomware. In RaaS assaults, the ransomware infrastructure is developed by cyber criminals after which licensed out to different attackers for his or her use. The client attackers will pay for using software program or they’ll break up the loot with the creators. Etay maor, Senior Director Safety Technique at Cato Networks commented, “There are different types of RaaS. After receiving the ransomware fee some Ransomware teams promote all the information concerning the sufferer’s community to different gangs. This implies the subsequent assault is way less complicated and might be totally automated because it doesn’t require weeks of discovery and community evaluation by the attackers.”
A few of the main RaaS gamers, who’re infamous for turning the RaaS panorama into what it’s at this time, are CryptoLocker, who contaminated over 1 / 4 million techniques within the 2000s and profited greater than $3 million in lower than 4 months, CryptoWall, who revamped $18 million and prompted an FBI advisory, and eventually Petya, NotPetya and WannaCry who used varied forms of exploits, ransomware included.
How the FBI Helps Fight Ransomware
A corporation underneath assault is sure to expertise frustration and confusion. One of many first beneficial programs of motion is to contact an Incident Response group. The IR group can help with investigation, recuperation and negotiations. Then, the FBI may assist.
A part of the FBI’s mission is to lift consciousness about ransomware. Because of a large native and world community, they’ve entry to priceless intelligence. This info may also help victims with negotiations and with operationalization. For instance, the FBI would possibly have the ability to present profiler details about a risk actor primarily based on its Bitcoin pockets.
To assist ransomware victims and to forestall ransomware, the FBI has arrange 56 Cyber Activity Forces throughout its area places of work. These Activity Forces work carefully with the IRS, the Division of Training, the Workplace of Inspector Common, the Federal Protecting Service and the State Police. They’re additionally in shut contact with the Secret Service and have entry to regional forensics labs. For Nationwide Safety cyber crimes, the FBI has a chosen Squad.
Alongside the Cyber Activity Drive, the FBI operates a 24/7 CyWatch, which is a Watch Heart for coordinating the sphere places of work, the non-public sector and different federal and intelligence businesses. There’s additionally an Web Crime Grievance Heart, ic3.gov, for registering complaints and figuring out traits.
Stopping Ransomware Assaults On Time
Many ransomware assaults do not have to achieve the purpose the place the FBI is required. Somewhat, they are often averted beforehand. Ransomware isn’t a single-shot assault. As an alternative, a collection of ways and methods all contribute to its execution. By figuring out the community and safety vulnerabilities prematurely that permits the assault, organizations can block or restrict risk actors’ potential to carry out ransomware. Etay Maor added “We have to rethink the idea that “the attackers must be proper simply as soon as, the defenders must be proper on a regular basis”. A cyber assault is a mix of a number of ways and methods. As such, it could actually solely be countered with a holistic strategy, with a number of converged safety techniques that every one share context in actual time. That is precisely what a SASE structure, and no different, affords the defenders”.
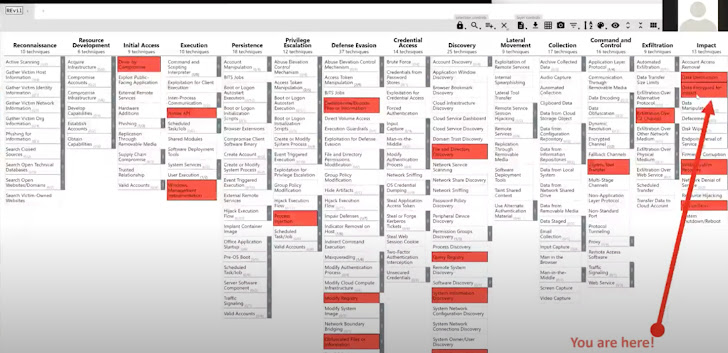
For instance, listed below are all of the steps in a REvil assault on a widely known producer, mapped out to the MITRE ATT&CK framework. As you may see, there are quite a few phases that passed off earlier than the precise ransom and had been important to its “success”. By mitigating these dangers, the assault may need been prevented.
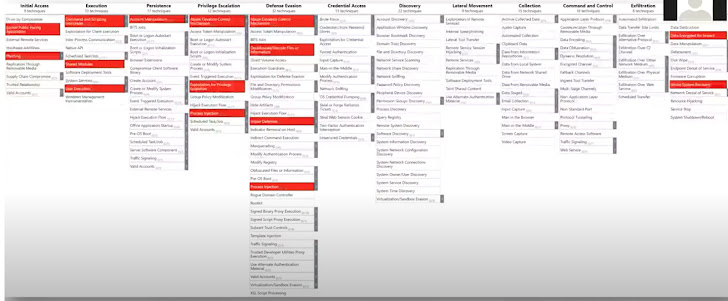
Here’s a related mapping of a Sodinokobi assault:
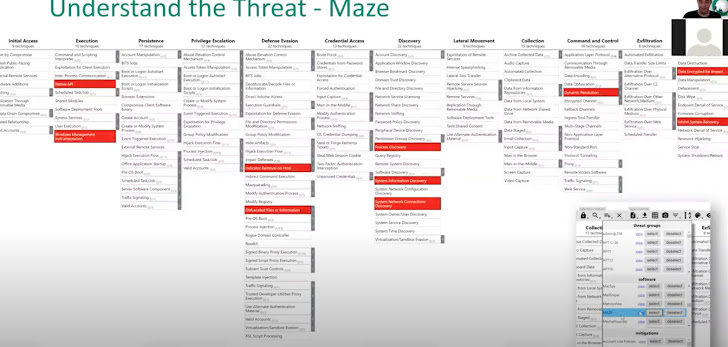
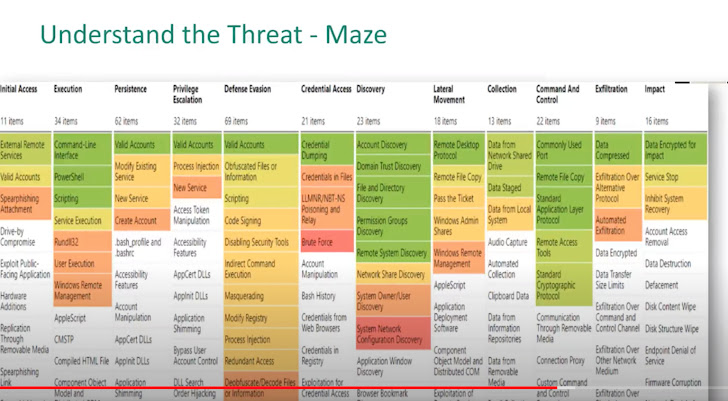
Maze assault mapping to the MITRE framework:
One other approach to map ransomware assaults is thru warmth maps, which present how usually completely different ways and methods are used. Here’s a warmth map of Maze assaults:
A method to make use of these mappings is for community evaluation and techniques testing. By testing a system’s resilience to those ways and methods and implementing controls that may mitigate any dangers, organizations scale back the danger of a ransomware assault by a sure actor on their vital sources.
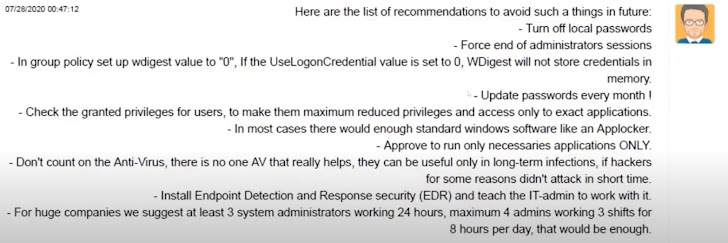
Keep away from Assaults – From the Horse’s Mouth
However do not take our phrase for it. Some ransomware attackers are “form” sufficient to offer organizations with greatest practices for securing themselves from future ransomware assaults. Suggestions embody:
- Turning off native passwords
- Utilizing safe passwords
- Forcing the top of admin periods
- Configuring group insurance policies
- Checking privileged customers’ entry
- Guaranteeing solely essential purposes are operating
- Limiting the reliance of Anti-Virus
- Putting in EDRs
- 24 hour system admins
- Securing susceptible ports
- Waiting for misconfigured firewalls
- And extra
Etay Maor of Cato Networks highlights “Nothing in what a number of Ransomware teams say organizations must do is new. These greatest practices have been mentioned for years. The explanation they nonetheless work is that we attempt to apply them utilizing disjoint, level options. That did not work and won’t work. A SASE, cloud native, structure, the place all safety options share context and have the potential to see each networks circulation and get a holistic view of the assault lifecycle can degree the enjoying area towards cyber assaults”.
Ransomware Prevention: An Ongoing Exercise
Identical to brushing your enamel or exercising, safety hygiene is an ongoing, methodical follow. Ransomware attackers have been identified to revisit the crime scene and demand a second ransom, if points have not been resolved. By using safety controls that may successfully mitigate safety threats and having a correct incident response plan in place, the dangers might be minimized, in addition to the attackers’ pay day. The FBI is right here to assist and supply info that may help, let’s hope that help will not be wanted.
To study extra about ransomware assaults and the best way to forestall them, Cato Networks’ Cyber Safety Masterclass collection is on the market to your viewing.