Cryptocurrency funding corporations are the goal of a creating menace cluster that makes use of Telegram teams to hunt out potential victims.
Microsoft’s Safety Risk Intelligence Middle (MSTIC) is monitoring the exercise beneath the identify DEV-0139, and builds upon a current report from Volexity that attributed the identical set of assaults to North Korea’s Lazarus Group.
“DEV-0139 joined Telegram teams used to facilitate communication between VIP shoppers and cryptocurrency alternate platforms and recognized their goal from among the many members,” the tech large mentioned.
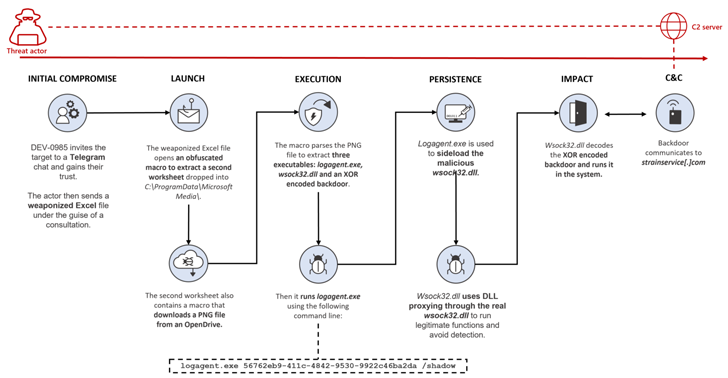
The adversary subsequently impersonated one other cryptocurrency funding firm and invited the sufferer to affix a distinct Telegram chat group beneath the pretext of asking for suggestions on the buying and selling payment construction utilized by alternate platforms throughout VIP tiers.
It is value mentioning that the VIP program is designed to reward high-volume merchants with unique buying and selling payment incentives and reductions primarily based on their crypto exercise previously 30 days.
This assault chain notably dovetails with Volexity’s evaluation of an October 2022 marketing campaign, whereby the menace actor pivoted from utilizing MSI installer information to a weaponized Microsoft Excel doc displaying the supposed cryptocurrency coin charges.
Microsoft described the doc as containing possible correct knowledge to extend the possibilities of success of the marketing campaign, suggesting that DEV-0139 is effectively versed with the interior workings of the cryptocurrency sector.
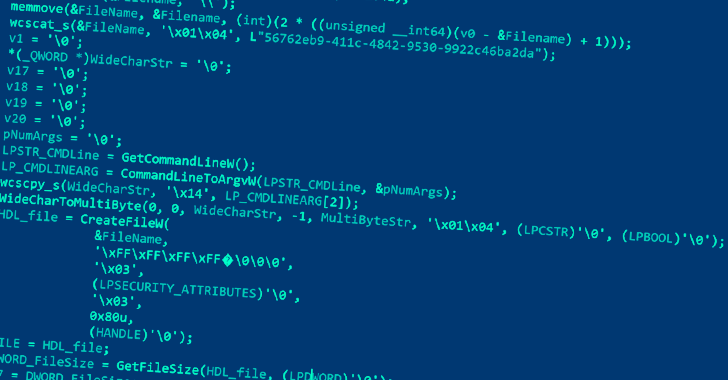
The malware-laced Excel file, for its half, is tasked with executing a malicious macro that is used to stealthily drop and execute a second Excel worksheet, which, in flip, features a macro that downloads a PNG picture file hosted on OpenDrive.
This picture file incorporates three executables, every of which is used to launch the next-stage payload, in the end paving the way in which for a backdoor that lets the menace actor remotely entry the contaminated system.
Moreover, the payment construction spreadsheet is password-protected in a bid to persuade the goal into enabling macros, thereby initiating the malicious actions. A metadata evaluation of the file exhibits that it was created on October 14, 2022 by a consumer named Wolf.
DEV-0139 has additionally been linked to another assault sequence during which an MSI bundle for a faux software named “CryptoDashboardV2” is delivered rather than a malicious Excel doc to deploy the identical implant.
The backdoor primarily allows distant entry to the host by gathering data from the focused system and connecting to a command-and-control (C2) server to obtain further instructions.
“The cryptocurrency market stays a discipline of curiosity for menace actors,” Microsoft mentioned. “Focused customers are recognized by way of trusted channels to extend the possibility of success.”
Lately, Telegram has not solely witnessed widespread adoption within the cryptocurrency trade, but in addition been co-opted by menace actors trying to talk about zero-day vulnerabilities, supply stolen knowledge, and market their companies by way of the favored messaging platform.
“With customers shedding confidence within the anonymity provided by boards, illicit marketplaces are more and more turning to Telegram,” Constructive Applied sciences disclosed in a brand new research of 323 public Telegram channels and teams with over a million subscribers in whole.
“The variety of distinctive cyberattacks is continually rising, and the marketplace for cybercriminal companies is increasing and transferring into peculiar social media and messaging apps, thereby considerably reducing the entry threshold for cybercriminals.”